|
1
|
The Biggest Cybersecurity Attacks Recorded |

|
Curious about the world of cybersecurity? To keep you informed, I have delved into the most massive cyber attacks ever recorded. Let's explore the critical incidents, their impact, and ways to stay protected together. By the end of this article, you'...
Author: Newton Waweru |
|
|
|
|
2
|
Email Setup: How To Set Up a Mail Server On Windows or Mac OS X |

|
Do you want to send and receive emails with your windows or Mac OS X and connect to it using a smartphone or PC? This guide is for you.
There are several ways you can set up a mail server on Mac OS X. For example, you can use server setting prefere...
Author: Faith Cheruiyot |
|
|
|
|
3
|
Email Migration Tips: How Does Email Migration Work? |

|
Do you want to migrate your email from one host to another? In the email industry, migration can sometimes be risky and needs a lot of attention to avoid problems. Before starting, knowing what to expect from the email migration process will help you...
Author: Faith Cheruiyot |
|
|
|
|
4
|
Email Migration: What Is The Purpose Of Email Migration? |

|
Want to migrate email from one host to another or hire someone? Before you start, it is good to understand the primary purposes of email migration. Knowing that will help you be in a position to understand the email industry to lead you into a smooth...
Author: Faith Cheruiyot |
|
|
|
|
5
|
How to clear my browser history |

|
Importance of clearing browser historyWhen you visit a website, your browser usually stores some information concerning the place, that is, the location of the site you visited, the file you have been using in running the application, and other downl...
Author: James Fleming |
|
|
|
|
6
|
What Is a Burner Phone, and When Should You Use One |

|
I have been wondering how a burner phone can be used or if it is necessary to have one. I am sure I'm not the only one with such questions, so I did my research and wrote this article on burner phones and in which instances they can be helpful to bot...
Author: Janet Kathalu |
|
|
|
|
7
|
How do I automatically print an email attachment? |

|
In the modern world, getting a reliable automated solution makes work easier and speeds up your workflow.
Have you been wondering how to print your email attachments automatically? In this article, we will guide you through several ways you can achi...
Author: Faith Cheruiyot |
|
|
|
|
8
|
How Do Search Engines Work? |

|
You’re in the kitchen making your mom’s favorite pizza. To get topping ideas, you open your web browser to perform a search. You type ‘topping ideas’ in the search box, hit ‘Enter,’ and get eighty-nine million results in about half a second. For th...
Author: Ian Musyoka |
|
|
|
|
9
|
How to Check If an Email Is Legit? |

|
“Phishing” is a popular term among hackers and hacking sites. These phishing emails are sent with the primary purpose of stealing valuable information or taking control of your networks.
It’s reported that every day nearly 3.4 billion phishing emai...
Author: Tithi Raha |
|
|
|
|
10
|
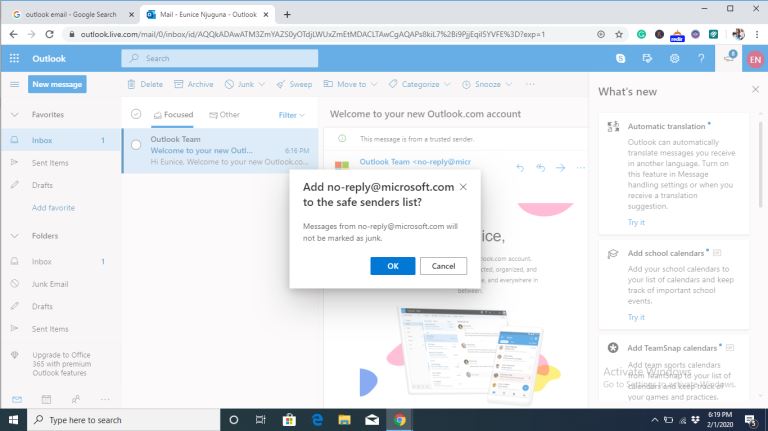
How Do I Stop Emails Going to Spam Folder |
|
Gmail, Yahoo, Hotmail, AOL, and Outlook are all excellent email services. They offer efficient email services by ensuring the proper delivery of emails to the inbox folder. But even with the efficiency in their services, there are negative issues tha...
Author: Eunice Njuguna |
|
|
|
|
11
|
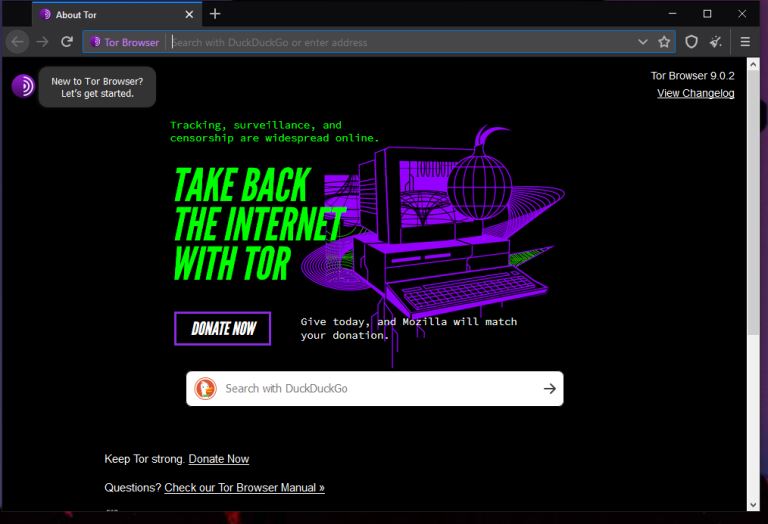
What is The Darknet? |
|
The US Department of Defense developed an encrypted and anonymized network in the late ‘90s. The intention behind developing this network was to operate a secure and inaccessible network that would offer absolute protection and shielding from US Gove...
Author: Collins Okoth |
|
|
|