|
1
|
What Does a Solid Access Control Policy Look Like |

|
Navigating the complexities of creating a robust access control policy can be challenging. This article will delve into the components of a solid access control policy, highlighting its importance in data protection and cybersecurity.
As a whole, a...
Author: Newton Waweru |
|
|
|
|
2
|
How Do Authentication Processes Work Decoding Security |

|
Hello there! The mechanics of digital authentication might seem complex. This is a vast topic, but I'm here to clarify it with my deep understanding. This article will delve into the functioning of authentication processes.
Authentication processes ...
Author: Newton Waweru |
|
|
|
|
3
|
Can Binary Code Be Used for Hacking? Uncover the Truth |

|
Are you eager to learn about the possibilities of using binary code for hacking? My comprehensive article explores the reality of binary code's capabilities in the realm of hacking.
In general, binary code can be applied as a technique in the field ...
Author: Newton Waweru |
|
|
|
|
4
|
Does Your Game Console Repair Pass The Test? Things You Can Improve |

|
Looking for game console repair services? Before you go ahead, here are some things you need to know before you get this service.
There are two ways to know if the game console repair meets the required parameters. The first and most important is t...
Author: Caroline Chebet |
|
|
|
|
5
|
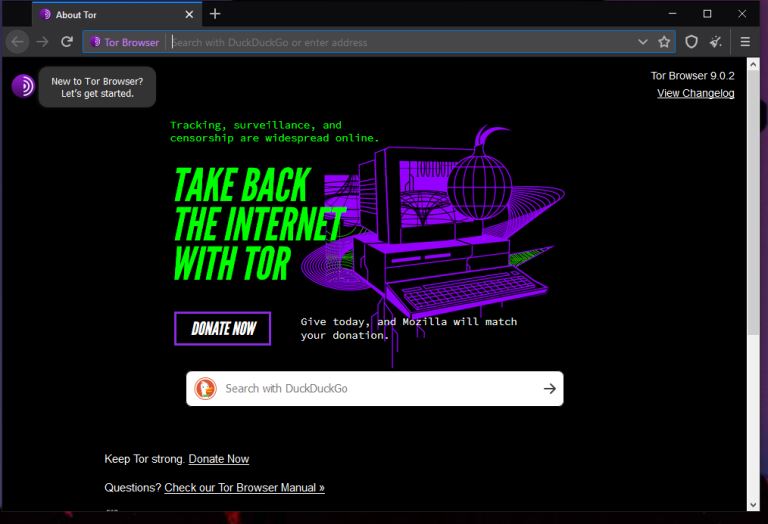
What is The Darknet? |
|
The US Department of Defense developed an encrypted and anonymized network in the late ‘90s. The intention behind developing this network was to operate a secure and inaccessible network that would offer absolute protection and shielding from US Gove...
Author: Collins Okoth |
|
|
|