|
1
|
How have Online Scams Evolved Cybersecurity and Digital Deception |

|
Understanding the evolution of online scams is essential in this digital age. As someone who has thoroughly studied this issue, I share your concerns about this complex and ever-changing problem. This article is here to help, presenting a detailed lo...
Author: Newton Waweru |
|
|
|
|
2
|
Common Misconceptions about Cybersecurity |

|
It seems like you're curious about common misconceptions surrounding cybersecurity. Don't worry. I'm here to help you navigate this topic. As someone who has researched this extensively, this article will shed light on the most prevalent misunderstan...
Author: Newton Waweru |
|
|
|
|
3
|
Emerging Trends and Challenges in Cybersecurity |

|
In today's rapidly evolving digital landscape, emerging trends and challenges in cybersecurity are of great concern. Together, we'll explore these trends and challenges, arming you with the knowledge to protect your digital assets. This article will ...
Author: Newton Waweru |
|
|
|
|
4
|
What Does a Solid Access Control Policy Look Like |

|
Navigating the complexities of creating a robust access control policy can be challenging. This article will delve into the components of a solid access control policy, highlighting its importance in data protection and cybersecurity.
As a whole, a...
Author: Newton Waweru |
|
|
|
|
5
|
What Does a VPN Do Securing Digital Privacy |

|
Navigating the digital world can feel like walking through a minefield. Leveraging years of research, we'll unravel how VPNs safeguard your online presence, preserving your privacy and security. Brace yourself for an informative journey into what a V...
Author: Newton Waweru |
|
|
|
|
6
|
What are the Challenges Faced in Cybersecurity Risks and Solutions |

|
Cybersecurity is a growing concern, and navigating its challenges can be daunting. You're not alone in seeking help; I'm here to provide the guidance you need. This article dives into the key obstacles faced in cybersecurity, offering practical insig...
Author: Newton Waweru |
|
|
|
|
7
|
What is the Importance of EndUser Education Boosting Security |

|
Navigating the digital realm can be a daunting task. This article will detail how user education aids in maximizing tech usability and boosting security. We're here to help you comprehend and apply this valuable knowledge.
As a whole, the importance...
Author: Newton Waweru |
|
|
|
|
8
|
How Does Malware Work Malware Definition Types and Protection |

|
I understand how troubling it can be to deal with the mysteries of cyber threats like malware. Fear not, as I've delved into the subject to help simplify it for you. In this article, we'll untangle the intricacies of malware, how it works, and its im...
Author: Newton Waweru |
|
|
|
|
9
|
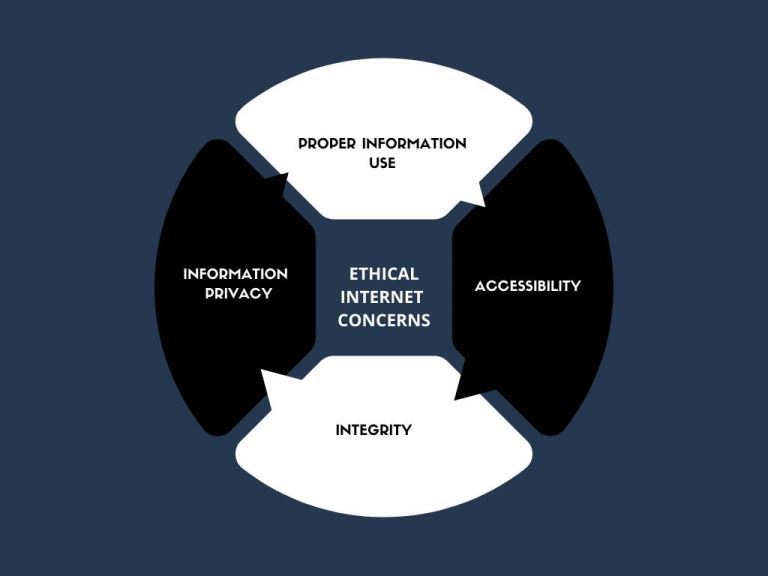
The Range and Scope of Internet Ethics A Comprehensive Guide |

|
Diving into the complex world of Internet Ethics? You're not alone! I've explored the range and scope of this topic to help you navigate these ethical dilemmas. This article will provide insights and guidance, ensuring you make informed decisions onl...
Author: Newton Waweru |
|
|
|
|
10
|
What are the 3 Main Pillars of Cybersecurity Internet Safety |

|
I understand cybersecurity can be complex and daunting, but don't worry - I'm here to help. As someone who has researched this topic extensively, I'll share the three main pillars of cybersecurity clearly and concisely, ensuring you gain a solid unde...
Author: Newton Waweru |
|
|
|
|
11
|
Methods You Can Use to Protect Yourself from Social Engineering |

|
With the digital world evolving, the risk of social engineering has become a concern for many. Leveraging our expertise, we can arm you with methods to protect yourself against social engineering threats. This article will detail effective strategies...
Author: Newton Waweru |
|
|
|
|
12
|
What is a Possible Effect of Malicious Code |

|
Navigating the digital world can feel like a labyrinth, especially when malicious code lurks in the shadows. It's alarming, I know. But fear not; I've delved into this complex issue to help guide you. In this article, we'll illuminate the potential e...
Author: Newton Waweru |
|
|
|
|
13
|
Types of Cybersecurity Threats Identifying Key Risks |

|
Cybersecurity threats are a growing concern in our digital age, and staying informed is essential. As someone who understands your need for help, I've delved into this topic to provide you with valuable insights. This article will cover various cyber...
Author: Newton Waweru |
|
|
|
|
14
|
How Can you Defend Yourself Against a Ransomware Attack |

|
Facing ransomware attacks can be terrifying, and we understand the anxiety it brings. Don't worry; I am here to help you defend yourself effectively. As someone who has delved into this issue, I've got your back. This article will provide actionable ...
Author: Newton Waweru |
|
|
|
|
15
|
Methods that Employees Can Expose Company Data Accidentally |

|
Concerned about employees accidentally exposing company data? You're not alone. I've delved into this issue, and I'm here to help. In this article, I'll explore standard methods that can lead to unintentional data leaks so that you can take preventiv...
Author: Newton Waweru |
|
|
|
|
16
|
The History of Cybersecurity and Hacking A Detailed Guide |

|
I understand your interest in the history of cybersecurity and hacking, as it's a fascinating subject. Rest assured, I've delved deeply into the topic and will guide you. This article will explore key milestones and developments that shaped this ever...
Author: Newton Waweru |
|
|
|
|
17
|
The Danger of Mixing Cyberwarfare with Cyber Espionage |

|
Are you concerned about the potential hazards of combining cyber warfare and cyber espionage? You're not alone. As someone who has delved deep into this critical issue, I understand your concerns and am here to help. This article will explore the ris...
Author: Newton Waweru |
|
|
|
|
18
|
How to Protect Yourself from Cyberstalking Stay Safe Online |

|
Are you concerned about cyberstalking and your online safety? You're not alone. As an individual who delved into this issue, I empathize with your worries. In this article, I'll discuss practical steps to protect yourself from cyberstalking, so you c...
Author: Newton Waweru |
|
|
|
|
19
|
How to Protect Your Company Against Cyber Espionage |

|
Concerned about cyber espionage threatening your business? You're not alone. As an experienced researcher, I understand the need to stay vigilant. In this article, I'll explore practical steps to safeguard your company, providing you with the tools t...
Author: Newton Waweru |
|
|
|
|
20
|
Cybersecurity Expectations vs Reality What You Need to Know |

|
Are you eager to learn about cybersecurity but feel overwhelmed by the jargon and technicalities? You're not alone, as many people find themselves navigating this intricate landscape with high expectations, only to be met with realities that often fe...
Author: Newton Waweru |
|
|
|
|
21
|
The Next Big Thing in Cyber Security Discover Innovative Solutions |

|
Ready to uncover the Next Big Thing in Cyber Security? You're not alone! As cyber threats evolve, so should our defenses. Fear not, I've delved deep into this crucial issue to help you stay informed and prepared. Join me in this article as we explore...
Author: Newton Waweru |
|
|
|
|
22
|
Font Meme Pictures there uses and how can I make them. |

|
Font Meme Pictures there uses and how can I make them.
Introduction
Font Meme Pictures are a creative way to express ideas and emotions through images. They consist of three main components: text, font, and color. This combination allows you to cre...
Author: James Fleming |
|
|
|
|
23
|
What iPad Repair Strategies You Should Try Today |

|
iPads are unique devices that have revolutionized the way we work and play. But like all electronic gadgets, they can sometimes malfunction or break. If your iPad needs repair, don't worry - you're not alone! Thousands of people each year find themse...
Author: Faith Cheruiyot |
|
|
|
|
24
|
Image Files: What Is a GIF, and How Do You Use Them |

|
Have you seen GIFs online or friends sharing them with you on social media platforms and have no idea how to use them? Worry not, GIFs are now part of social life, and it's an awesome idea to know everything there is to know about GIFS and, most impo...
Author: Janet Kathalu |
|
|
|
|
25
|
What Are Ethical and Unethical Practices Related to Internet Use? |
|
Information technology has made the world more accessible than ever in history. Different people from different parts of the world have the ability to access the internet and simultaneously make use of online resources. Do not be deceived that what...
Author: Ian Musyoka |
|
|
|
|
26
|
Why Do We Need Ethics for Internet Users? |

|
With the introduction of computers globally in the 1990s, the entire approach of working, communicating, and storing important information has changed. I mean, who would have thought that a machine can make one convey a message at any corner of the w...
Author: Collins Okoth |
|
|
|