|
1
|
How Does Malware Work Malware Definition Types and Protection |

|
I understand how troubling it can be to deal with the mysteries of cyber threats like malware. Fear not, as I've delved into the subject to help simplify it for you. In this article, we'll untangle the intricacies of malware, how it works, and its im...
Author: Newton Waweru |
|
|
|
|
2
|
What are the 3 Main Pillars of Cybersecurity Internet Safety |

|
I understand cybersecurity can be complex and daunting, but don't worry - I'm here to help. As someone who has researched this topic extensively, I'll share the three main pillars of cybersecurity clearly and concisely, ensuring you gain a solid unde...
Author: Newton Waweru |
|
|
|
|
3
|
What Did the End of Net Neutrality Mean Policies and Controversy |

|
Hey there, I understand the end of net neutrality can be a complex issue to grasp. Fear not, I've delved deep into this topic to make things clear for you. This article will explore the implications of net neutrality's demise, its impact on the inter...
Author: Newton Waweru |
|
|
|
|
4
|
What is the Controversy that Destroyed Net Neutrality |

|
Hey there, you're curious about the controversy that led to the destruction of net neutrality. I can relate, as it's a complex topic with many opinions. I've thoroughly researched and am confident I can help clarify things for you. This article will ...
Author: Newton Waweru |
|
|
|
|
5
|
Types of Intrusion Detection Systems Host and Network |

|
You've come to the right place to learn about the various types of Intrusion Detection Systems (IDS). This article will provide a comprehensive overview of the different IDS types, ensuring you're well-equipped to make an informed decision.
In total...
Author: Newton Waweru |
|
|
|
|
6
|
How Do Transistors Store Binary Data? Understand How Transistors Work |

|
Are you curious about how transistors store binary data? I'm here to help you understand how transistors work and demystify this topic. Get ready to dive deep into the workings of transistors and discover how these tiny components play a crucial role...
Author: Newton Waweru |
|
|
|
|
7
|
Controlling and Viewing devices connected to your Wi-Fi Network |

|
It's worth taking the time to see who is connected to your Wi-Fi network. Your home network security could be compromised if unauthorized users are piggybacking on your connection, slowing down your speeds and using up your data - all without you k...
Author: James Fleming |
|
|
|
|
8
|
Why can't I see other computers on my network Mac? |

|
Why can't I see other computers on my network Mac?
The most challenging aspect of connecting to a network is getting all the computers on the same page. It can be a frustrating experience if you can't see other machines on your Mac network. Fortunat...
Author: James Fleming |
|
|
|
|
9
|
How Can I Tell If I Need a New Router? Here Are The Signs! |

|
Wi-Fi router plays one of the most crucial roles when creating and sending out Wi-Fi signal across the home. Without having a seamless router, your devices such as your tablet, smartphone, or PC won't be connected to the wireless network setup. Altho...
Author: Tithi Raha |
|
|
|
|
10
|
How Can I Make My Internet Run Faster? Check Out The Practical Ways! |

|
Are you tired of the constant buffering of videos? Or is your webpage taking forever to load? Well, you're not alone. Slow internet connection is a problem that everyone encounters at some point in their life and it drives them nuts. After all, most ...
Author: Tithi Raha |
|
|
|
|
11
|
Is Download Slower Than Upload? Why & How to Fix it? |

|
In today's age, it's inevitable to have a good internet connection not only for gamers but also for ordinary people. So, you opt for a suitable plan from your internet service provider, each offering a variety of upload and download speeds. But, your...
Author: Tithi Raha |
|
|
|
|
12
|
Smart Security System: Protecting Your Home From Burglars |

|
Like most people, you probably think of your home as your sanctuary. It's where you feel safe and secure, and it's a refuge from the hustle and bustle of the outside world. But what happens when a burglary shatters that sense of safety? A smart secur...
Author: Faith Cheruiyot |
|
|
|
|
13
|
How to Configure Email Client To Send Mail Through My Own SMTP Server? |

|
SMTP is the internet standard for sending and receiving emails. Email clients use SMTP to send messages to a mail server, while email servers use it to forward messages to their recipients. You need to enter your SMTP settings to use the email from a...
Author: Faith Cheruiyot |
|
|
|
|
14
|
Custom PC Build: How hard is it to build a PC? |

|
Are you aspiring to build your PC or hire someone? Don't worry; it is never hard, and you only need the skills and assembling of parts. Before starting off, ensure you understand all the rules of assembling a PC to make it easier.
There are many way...
Author: Faith Cheruiyot |
|
|
|
|
15
|
Tablet Repair: Common Tablet Problems And Solutions |

|
After spending so much money on your new tablet, the expectations are always high. Many users dont have expectations of getting problems, thats not the reality. Tablet users experience several problems, and there are ways one can fix them.
The are ...
Author: Faith Cheruiyot |
|
|
|
|
16
|
Why Does My Radio Stereo Turn On But No Sound? |

|
Is your radio turning on but has no sound? Are you wondering how to fix a radio stereo with no sound? It could be a problem with the antenna, speaker, amplifier, or connectivity of wires. Check the radio functions to ensure your audio source is conne...
Author: Faith Cheruiyot |
|
|
|
|
17
|
What are the simple and fast fixes for Android Repair |

|
Android issues are a common thing that one must experience once in a while. The issues would be less stressful if you knew how to fix them, and this article is just the right place for you to find out the simple and fast fixes to aid you in android r...
Author: Nancy Museo |
|
|
|
|
18
|
How to Hard Refresh Your Web Browser (to Bypass Your Cache) |

|
How to Hard Refresh Your Web Browser (to Bypass Your Cache) is a wide topic. You must have come across a person who requests you to consider clearing the browser cache. If this is the case, you need this specific diagnostic, especially in the case w...
Author: James Fleming |
|
|
|
|
19
|
Methods to Fix No Bootable Device on Windows 10 |

|
If you are experiencing the 'no bootable device' error on your PC, it's likely that you have a hardware issue. It could also be a software misconfiguration that needs to be addressed. Whatever the case, these solutions will help fix it. The ideas wor...
Author: Eunice Njuguna |
|
|
|
|
20
|
Does private browsing actually work? |

|
With today's advanced technology, targeted ads and recommendation algorithms leave no space for privacy online. In line with this, you could expect your 'private' surfing through incognito mode to stay private, whereby you can remain anonymous. Howev...
Author: Collins Okoth |
|
|
|
|
21
|
Can My Employer Monitor My Work Computer At Home? |

|
An employer has every right to monitor the work computers of their employees at home. The employer will do so for various reasons: they will need to ensure their employees' productivity. It is also for the protection of the organization's software ...
Author: Gloria Mutuku |
|
|
|
|
22
|
How to stop a computer from overheating when playing games? |

|
As an avid gamer, you've probably spent thousands of dollars on a high-end gaming rig. So imagine your disappointment when your Desktop PC freezes or even shuts down abruptly mid-game.
The culprit here is most likely to be overheating. While modern ...
Author: Ujunwa Chibuzor |
|
|
|
|
23
|
A Detailed Guide to Removing Ransomware in Windows 10 |
|
One of the main problems faced by internet companies today is Ransomware. For this reason, cybersecurity has continued to grow as an industry in general. Unfortunately, players on both sides can easily be described as the bad guys and the good guys. ...
Author: Collins Okoth |
|
|
|
|
24
|
I Can't Open Email Attachments |

|
Email attachments are the files you receive alongside your email messages. The files come in different formats. The most common and widely used are the .pdf, .doc, .zip, or .html.
There are various other forms, and each requires specific computer p...
Author: Eunice Njuguna |
|
|
|
|
25
|
Computer Maintenance: How Do I Keep My Laptop Battery in Good Health? |

|
Image: A Laptop and Its Battery
The health of all batteries decreases over time with repeated charging and use, but this does not happen at the same speed. If you are given the same brand-new laptop on the exact day as someone else, the battery li...
Author: Ian Musyoka |
|
|
|
|
26
|
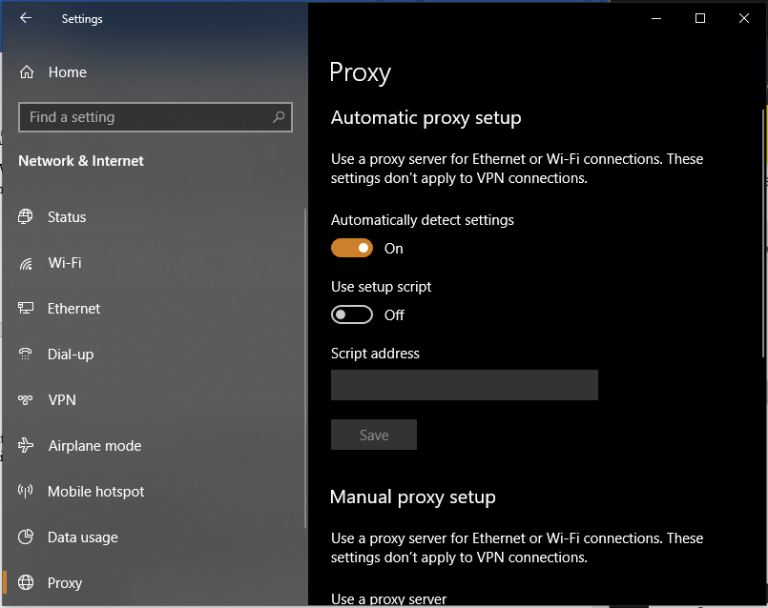
What are Proxy Server Ports? |
|
Proxy servers are dedicated software systems that run on a computer and are intermediaries between two endpoint devices. These endpoint devices are usually a personal computer and a server. A server is a central computer from which other computers (c...
Author: Collins Okoth |
|
|
|
|
27
|
How to Remove Malicious Software |

|
Malware is software designed to damage, gain access to, or disrupt the normal functioning of the computer. Malware is valuable to cybercriminals because they use it to extract sensitive information, prevent access to the device, and steal money. The ...
Author: Delilah Daut |
|
|
|
|
28
|
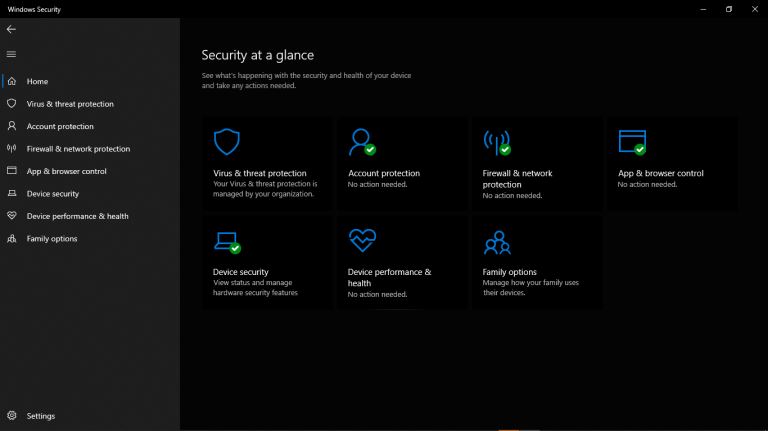
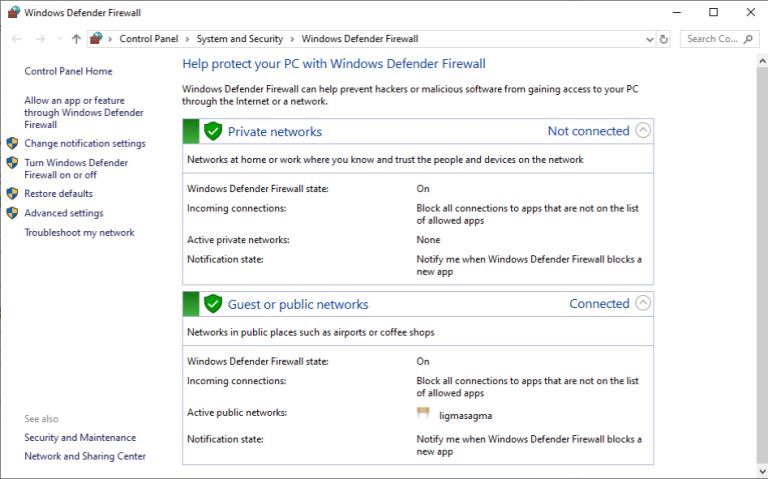
What Does a Firewall Do? |
|
Before I started writing this, I thought to myself, “Who really needs a firewall?” But, as it turns out, most of us do. If your personal or company computer is connected to the internet, your network is always exposed to threats and risks. This mea...
Author: Ian Musyoka |
|
|
|
|
29
|
How To Replace a Motherboard |

|
Simple as it may sound, replacing a motherboard is a complex process. If you think of it from disassembling your computer, replacing a motherboard is like half the task. It is time-consuming, and both experienced and inexperienced people require seve...
Author: Eunice Njuguna |
|
|
|
|
30
|
How To Clear Your Cache |

|
If you've ever struggled to access specific websites or failed to load an image on a webpage, no matter how many times you hit refresh, you've probably been advised to “clear your cache.” In fact, the only phrase more common in the world of IT and te...
Author: Trey Williams |
|
|
|