|
1
|
Methods that Employees Can Expose Company Data Accidentally |

|
Concerned about employees accidentally exposing company data? You're not alone. I've delved into this issue, and I'm here to help. In this article, I'll explore standard methods that can lead to unintentional data leaks so that you can take preventiv...
Author: Newton Waweru |
|
|
|
|
2
|
The Danger of Mixing Cyberwarfare with Cyber Espionage |

|
Are you concerned about the potential hazards of combining cyber warfare and cyber espionage? You're not alone. As someone who has delved deep into this critical issue, I understand your concerns and am here to help. This article will explore the ris...
Author: Newton Waweru |
|
|
|
|
3
|
How Can an Intrusion Detection System Protect Your Company |

|
Concerned about your company's cybersecurity? An Intrusion Detection System (IDS) might be your perfect solution. I understand how critical it is to protect sensitive data, and I've delved into the topic to provide the guidance you need.
An intrusi...
Author: Newton Waweru |
|
|
|
|
4
|
How to Protect Your Company Against Cyber Espionage |

|
Concerned about cyber espionage threatening your business? You're not alone. As an experienced researcher, I understand the need to stay vigilant. In this article, I'll explore practical steps to safeguard your company, providing you with the tools t...
Author: Newton Waweru |
|
|
|
|
5
|
Things Every Employee Should Know about Cybersecurity Safety Tips |

|
Struggling with cybersecurity at work? You're not alone. As an employee, it's crucial to understand the basics of online safety. I've delved into the topic and can help you navigate this complex world. In this article, I'll explore key cybersecurity ...
Author: Newton Waweru |
|
|
|
|
6
|
Cybersecurity Expectations vs Reality What You Need to Know |

|
Are you eager to learn about cybersecurity but feel overwhelmed by the jargon and technicalities? You're not alone, as many people find themselves navigating this intricate landscape with high expectations, only to be met with realities that often fe...
Author: Newton Waweru |
|
|
|
|
7
|
The Next Big Thing in Cyber Security Discover Innovative Solutions |

|
Ready to uncover the Next Big Thing in Cyber Security? You're not alone! As cyber threats evolve, so should our defenses. Fear not, I've delved deep into this crucial issue to help you stay informed and prepared. Join me in this article as we explore...
Author: Newton Waweru |
|
|
|
|
8
|
What Is Cloud Computing as a Form of Technology Today |

|
In a nutshell, this article explains how Cloud Computing Is being used Today, as well as It's benefits.
As a whole, Cloud Computing Is the ability to access Information on the Internet with ease ,via the different applications enabled by the cloud b...
Author: Rahab Nyambura |
|
|
|
|
9
|
What Does a Computer Repair Topeka KS Technicians Do |

|
Computer Repair Topeka, KS technicians perform all the necessary steps to repair the malfunctioning computer software and hardware. Upon calling a technician, they will first diagnose the issues with your computer system and ensure all are returned t...
Author: Tithi Raha |
|
|
|
|
10
|
What is The Difference Between Computer Repair Technicians & Help Desk |

|
When it comes to the help desk analyst and computer repair Topeka, KS technician, people often need clarification on these two. Regardless of how similar these two sound, they have significant differences. However, both of them are designed to help c...
Author: Tithi Raha |
|
|
|
|
11
|
How to Select The Best Computer Repair Shop in Topeka, KS |

|
When you're dealing with computer issues requiring a professional's help, it's essential to make sure that you choose the ideal Computer Repair in Topeka, Kansas, or any other area to avoid major damages or unfavorable situations. Hiring the wrong re...
Author: Tithi Raha |
|
|
|
|
12
|
Can Binary Code Be Used for Hacking? Uncover the Truth |

|
Are you eager to learn about the possibilities of using binary code for hacking? My comprehensive article explores the reality of binary code's capabilities in the realm of hacking.
In general, binary code can be applied as a technique in the field ...
Author: Newton Waweru |
|
|
|
|
13
|
What Security Parameters are Present in the Cloud? |

|
The security parameters present in the cloud are the technologies designed to counter internal and external threats. They include data loss prevention applications, disaster recovery tools, and identity access management systems. Most cloud security ...
Author: Eunice Njuguna |
|
|
|
|
14
|
What Workloads Can be Moved to The Cloud? |

|
The migration of workloads involves the transfer of virtual machines, software, or databases to the cloud. The migration characterizes the selection of existing workloads, changing them, and deploying them to a cloud platform. Most businesses move wo...
Author: Eunice Njuguna |
|
|
|
|
15
|
How Can I Tell If Cloud Computing Is Right For My Company? |

|
Cloud computing is right for you if your company needs support with data storage, infrastructure scaling, big data analytics, networking, backup service strategies, and application development. A business looking to boost productivity, create room fo...
Author: Eunice Njuguna |
|
|
|
|
16
|
Font Meme Pictures there uses and how can I make them. |

|
Font Meme Pictures there uses and how can I make them.
Introduction
Font Meme Pictures are a creative way to express ideas and emotions through images. They consist of three main components: text, font, and color. This combination allows you to cre...
Author: James Fleming |
|
|
|
|
17
|
Email Migration Tips: How Does Email Migration Work? |

|
Do you want to migrate your email from one host to another? In the email industry, migration can sometimes be risky and needs a lot of attention to avoid problems. Before starting, knowing what to expect from the email migration process will help you...
Author: Faith Cheruiyot |
|
|
|
|
18
|
What Are The Modern Rules of In-home Computer Service? |

|
In the olden days, if your computer crashed or stopped working, you had to take it in for servicing. But now, with so many people working remotely and relying on their computers, there are new rules for when and how you should get your computer servi...
Author: Faith Cheruiyot |
|
|
|
|
19
|
How In-home Computer Service Is Important to You |

|
There's no doubt that having a computer is important in this day and age. However, what happens when your computer breaks? Chances are you might not have the money to take it in for repair, or maybe you don't have the time to wait for it to be fixed....
Author: Faith Cheruiyot |
|
|
|
|
20
|
10 Undeniable Benefits of Remote Assistance |

|
Advancements in technology have led to several changes in how we live and work. One of the most significant changes has been the rise of remote working. With the ability to connect to the internet from anywhere in the world, more and more people are ...
Author: Faith Cheruiyot |
|
|
|
|
21
|
What is the Best Software for Making Video Tutorials? |

|
Are you planning to make video tutorials? Do you want to explain how your products and services function using the software? Video Tutorial software is ideal as it lets you edit, generate, manipulate and enhance videos. Such ensures the corporate and...
Author: Faith Cheruiyot |
|
|
|
|
22
|
Monitor Repair: How Can I Discard Monitor Screen Safely |

|
Have you ever wondered how to dispose of an old computer monitor screen properly? If so, you're not alone. With the growing amount of electronic waste, it's important to know how to safely recycle or discard items like screens.
There are several way...
Author: Faith Cheruiyot |
|
|
|
|
23
|
Things You Didn't Know About Backup Services [What Are They?] |

|
A good backup service is crucial for ensuring all your data is safe from hardware failure or accidental deletion. Backup services offer companies and individuals the protection they need to keep their data safe. With backup services, companies can co...
Author: Faith Cheruiyot |
|
|
|
|
24
|
How to Electronically Sign PDFs Without Printing and Scanning Them |

|
You've been emailed a PDF document, which you must sign and return. You could print the document, sign it, then scan and email it back. However, there is a better, faster way. I'll demonstrate how to quickly add your signature to any PDF document and...
Author: Fay Kokri |
|
|
|
|
25
|
Why is my download speed so slow when I have fast internet? |

|
If your internet connection is fast but your internet download speed is slow, you can follow the workarounds below to resolve the issue.
There are several reasons why the internet may seem slow even if you have a high-speed internet connection. Re...
Author: Fay Kokri |
|
|
|
|
26
|
Cyberstalking and How to Protect Yourself From Identity Theft |

|
Image: Internet Security
Creating a better online experience in the data and communication field has become a non-negotiable topic. Given the current move into the digital space, advanced data platforms and new communication channels have been cre...
Author: Ian Musyoka |
|
|
|
|
27
|
Can You Get a Keylogger Just by Visiting a Website? |

|
Ever since malware and virus infections have started to increase at a rapid pace, the fear of getting a keylogger just by visiting a website is bothering many people. After all, a majority of internet users access a lot of websites on a daily basis. ...
Author: Tithi Raha |
|
|
|
|
28
|
What Does a VPN Hide? |

|
The more we use the internet, the more susceptible we become to cyber attacks. This makes a virtual private network (VPN) an essential tool to access the freedom of privacy when visiting streaming services, websites, and other places of interest on...
Author: Ian Musyoka |
|
|
|
|
29
|
How to Check If an Email Is Legit? |

|
“Phishing” is a popular term among hackers and hacking sites. These phishing emails are sent with the primary purpose of stealing valuable information or taking control of your networks.
It’s reported that every day nearly 3.4 billion phishing emai...
Author: Tithi Raha |
|
|
|
|
30
|
Can My Employer Monitor My Work Computer At Home? |

|
An employer has every right to monitor the work computers of their employees at home. The employer will do so for various reasons: they will need to ensure their employees' productivity. It is also for the protection of the organization's software ...
Author: Gloria Mutuku |
|
|
|
|
31
|
What is the Internet of Things IoT |

|
The Internet of things (IoT) is a general term for the increasing number of electronics that are not conventional computer equipment but connected to the Internet to send information, receive instructions, or both.
Tech analyst company IDC forecasts...
Author: Collins Okoth |
|
|
|
|
32
|
What is Ransomware How it Works and How to Remove it |

|
Ransomware has grabbed the attention of many internet users, governments, and internet companies in recent years. Although Ransomware has been in existence for a long time, its effects have continued to be felt. Ransomware is short for Ransom Malware...
Author: Collins Okoth |
|
|
|
|
33
|
I Can't Open Email Attachments |

|
Email attachments are the files you receive alongside your email messages. The files come in different formats. The most common and widely used are the .pdf, .doc, .zip, or .html.
There are various other forms, and each requires specific computer p...
Author: Eunice Njuguna |
|
|
|
|
34
|
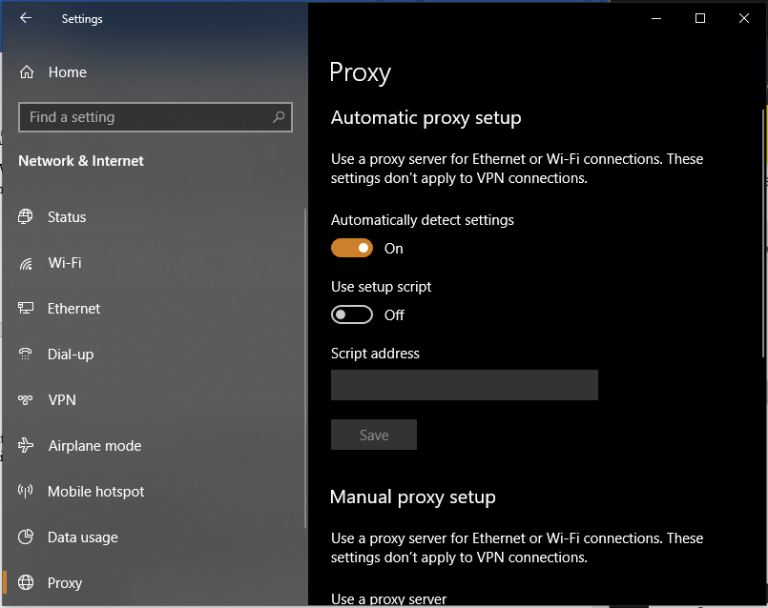
What are Proxy Server Ports? |
|
Proxy servers are dedicated software systems that run on a computer and are intermediaries between two endpoint devices. These endpoint devices are usually a personal computer and a server. A server is a central computer from which other computers (c...
Author: Collins Okoth |
|
|
|
|
35
|
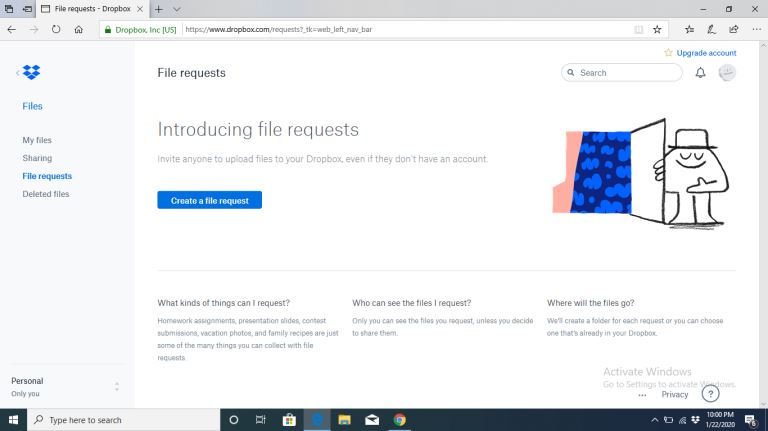
How Does Cloud Sharing Work |
|
Whether you are a business dealing with loads of information or an individual saving personal files, data is an integral part of day-to-day activities. Handling data is a standard process, and as you collect, save, and share information, it is essent...
Author: Eunice Njuguna |
|
|
|