|
1
|
What Methods Does HTTPS use that make it more secure than HTTP |

|
Navigating the digital landscape, it's essential to understand web security. Recognizing this, you want to explore HTTPS and its edge over HTTP. With my extensive cybersecurity knowledge, I'll help demystify this complex topic. This article focuses o...
Author: Newton Waweru |
|
|
|
|
2
|
What Does a VPN Do Securing Digital Privacy |

|
Navigating the digital world can feel like walking through a minefield. Leveraging years of research, we'll unravel how VPNs safeguard your online presence, preserving your privacy and security. Brace yourself for an informative journey into what a V...
Author: Newton Waweru |
|
|
|
|
3
|
How Does Malware Work Malware Definition Types and Protection |

|
I understand how troubling it can be to deal with the mysteries of cyber threats like malware. Fear not, as I've delved into the subject to help simplify it for you. In this article, we'll untangle the intricacies of malware, how it works, and its im...
Author: Newton Waweru |
|
|
|
|
4
|
Types of Cybersecurity Threats Identifying Key Risks |

|
Cybersecurity threats are a growing concern in our digital age, and staying informed is essential. As someone who understands your need for help, I've delved into this topic to provide you with valuable insights. This article will cover various cyber...
Author: Newton Waweru |
|
|
|
|
5
|
Understanding SSID: What Is It and How Does It Work? |

|
Understanding SSID: What Is It and How Does It Work?
Wireless networks have become increasingly popular, enabling people to connect to the Internet and access network resources without the need for wired connections. One of the key components of wir...
Author: James Fleming |
|
|
|
|
6
|
How to Detect Hidden Surveillance Cameras With Your Phone |

|
How to Detect Hidden Surveillance Cameras With Your Phone
Have you ever suspected that you were being watched but couldn't find any visible surveillance cameras? It's possible that the camera or cameras were hidden, making it difficult to detect the...
Author: James Fleming |
|
|
|
|
7
|
How To Protect the phone From Hackers Using Smart Security at Home app |

|
Every day, there's a new headline about a major company being hacked. While it's important to keep up with the latest security news, it's also essential to know how to protect your devices from hackers and scammers.
There are many ways hackers can g...
Author: Faith Cheruiyot |
|
|
|
|
8
|
How In-home Computer Service Is Important to You |

|
There's no doubt that having a computer is important in this day and age. However, what happens when your computer breaks? Chances are you might not have the money to take it in for repair, or maybe you don't have the time to wait for it to be fixed....
Author: Faith Cheruiyot |
|
|
|
|
9
|
How Can I Hack Someone's Wireless Network? |

|
Wireless networks or Wi-Fi are usually accessible to everyone who is within the transmission radius. You can use the hotspots in public places like restaurants, airports, parks, etc. This makes them more vulnerable to cyber-attacks. In fact, cracking...
Author: Tithi Raha |
|
|
|
|
10
|
Is It Possible That VPNs Will Slow Down Your Internet? |

|
When your Wi-Fi is running at a snail's pace, nothing can seem more frustrating than that. It's nearly impossible to work, play games, watch videos and even at worst you can't even send messages to your loved ones. This scenario should not be a surpr...
Author: Tithi Raha |
|
|
|
|
11
|
What are the dos and don'ts for a new computer setup? |

|
If you got a new computer and wondering what you should do or not do, you are in the right place. This guide has all the information you need to have a seamless new computer setup
There are several dos and donts when setting up and new computer. Yo...
Author: Caroline Chebet |
|
|
|
|
12
|
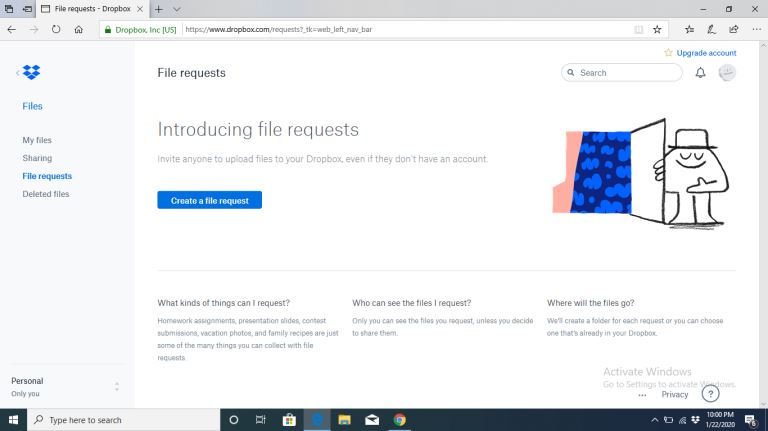
What is the best way to use cloud storage? |

|
Cloud storage is a data storage service sought by individuals and businesses. If you have large volumes of data that you are concerned about its safety and wish to retrieve whenever needed, cloud storage would be the best option for you. Are you new ...
Author: Gloria Mutuku |
|
|
|
|
13
|
What is HTTPs, and Why Should I Care about it? |

|
Most people often confuse HTTP and HTTPs, some think they can be used interchangeably, and so on. However, there is a simple and clear difference between HTTP and HTTPs in computer networking. Simply put, HTTPs is an abbreviation for Secure Hypertex...
Author: Collins Okoth |
|
|
|
|
14
|
What Is End-to-End Encryption in Messenger? |

|
Messenger has brought about a lot of privacy and safety tools in the past year. Some of these are app locks, disappearing messages, privacy settings, and message forwarding limits. However, the end-to-end encryption feature is still being worked on. ...
Author: Collins Okoth |
|
|
|
|
15
|
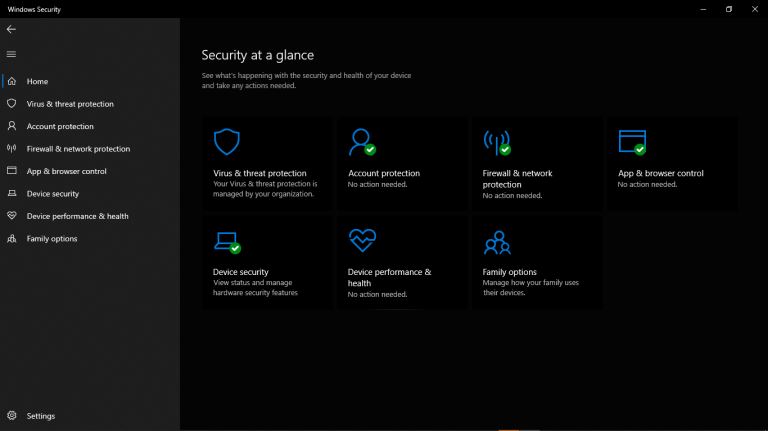
A Detailed Guide to Removing Ransomware in Windows 10 |
|
One of the main problems faced by internet companies today is Ransomware. For this reason, cybersecurity has continued to grow as an industry in general. Unfortunately, players on both sides can easily be described as the bad guys and the good guys. ...
Author: Collins Okoth |
|
|
|
|
16
|
What is Ransomware How it Works and How to Remove it |

|
Ransomware has grabbed the attention of many internet users, governments, and internet companies in recent years. Although Ransomware has been in existence for a long time, its effects have continued to be felt. Ransomware is short for Ransom Malware...
Author: Collins Okoth |
|
|
|
|
17
|
How Does Cloud Sharing Work |
|
Whether you are a business dealing with loads of information or an individual saving personal files, data is an integral part of day-to-day activities. Handling data is a standard process, and as you collect, save, and share information, it is essent...
Author: Eunice Njuguna |
|
|
|
|
18
|
What's Wrong With Using Public Wi-Fi? |

|
Picture yourself in your favorite cafe, drinking a hot cup of coffee while taking advantage of the free Wi-Fi to update your feed or keep up with the news. I bet that to some of us, and this already sounds like a very familiar setting. However, did...
Author: Ian Musyoka |
|
|
|
|
19
|
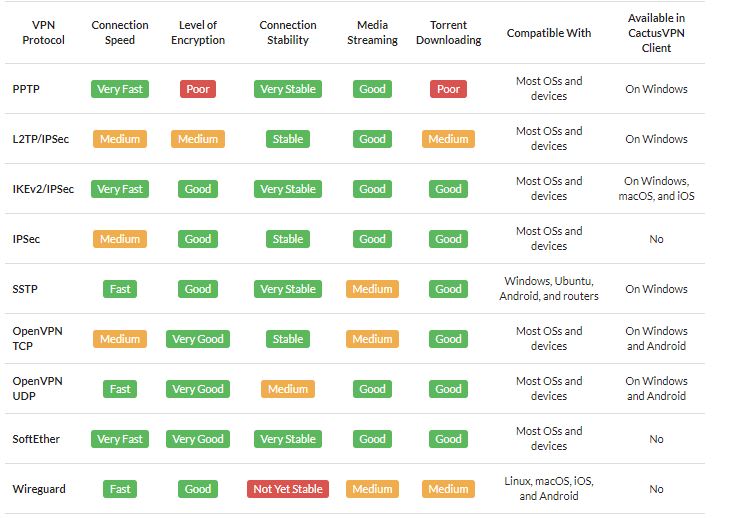
What Is a VPN? |
|
A VPN is short for Virtual Private Network. It is a collection of several networking schemes that allow computers to utilize public internet lines by creating a virtual network. VPNs have no specific standard models; however, it typically uses the pu...
Author: Collins Okoth |
|
|
|
|
20
|
How Do I Know If I Have a Virus on My Laptop or Desktop Computer |
|
Making sure you have up-to-date anti-virus software installed is the easiest way of protecting your computer against viruses. This software is usually the first to notice that something is wrong. But with malware and hackers getting ever more sophist...
Author: Trey Williams |
|
|
|