|
1
|
How have Online Scams Evolved Cybersecurity and Digital Deception |

|
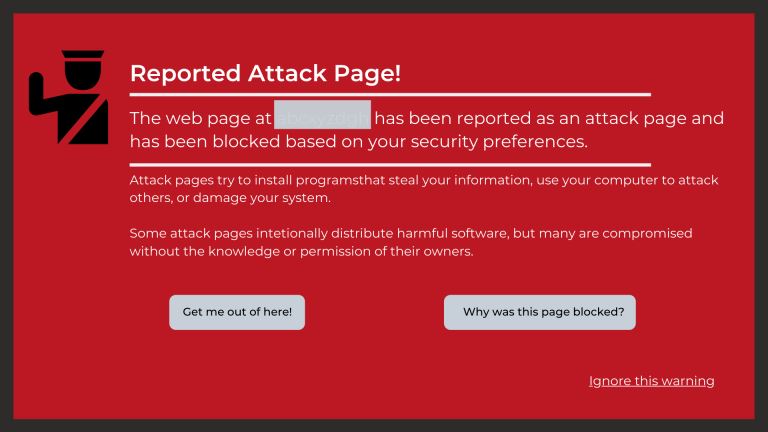
Understanding the evolution of online scams is essential in this digital age. As someone who has thoroughly studied this issue, I share your concerns about this complex and ever-changing problem. This article is here to help, presenting a detailed lo...
Author: Newton Waweru |
|
|
|
|
2
|
What Is the Importance of Having a Strong Password Digital Protection |

|
Navigating the digital world, you may often wonder, "Why are strong passwords so crucial?" Passwords are your digital keys, guarding personal information and online identities. In this article, we'll delve into the importance of robust passwords to ...
Author: Newton Waweru |
|
|
|
|
3
|
What is the Importance of EndUser Education Boosting Security |

|
Navigating the digital realm can be a daunting task. This article will detail how user education aids in maximizing tech usability and boosting security. We're here to help you comprehend and apply this valuable knowledge.
As a whole, the importance...
Author: Newton Waweru |
|
|
|
|
4
|
What are the 10 Commandments of Computer Ethics |

|
Navigating the digital world with respect and integrity is essential. As an expert in computer ethics, I've delved into the 10 Commandments of Computer Ethics, the cornerstone of responsible digital behavior. This article aims to help you better und...
Author: Newton Waweru |
|
|
|
|
5
|
Types of Cybersecurity Threats Identifying Key Risks |

|
Cybersecurity threats are a growing concern in our digital age, and staying informed is essential. As someone who understands your need for help, I've delved into this topic to provide you with valuable insights. This article will cover various cyber...
Author: Newton Waweru |
|
|
|
|
6
|
The Biggest Cybersecurity Attacks Recorded |

|
Curious about the world of cybersecurity? To keep you informed, I have delved into the most massive cyber attacks ever recorded. Let's explore the critical incidents, their impact, and ways to stay protected together. By the end of this article, you'...
Author: Newton Waweru |
|
|
|
|
7
|
What is the Importance of Internet Ethics Responsible Online Behavior |

|
Navigating the digital world, internet ethics is a vital topic you're not alone in exploring. I've got you covered. I empathize with your quest for guidance, and in this article, I'll discuss the importance of ethical conduct online, privacy, and sec...
Author: Newton Waweru |
|
|
|
|
8
|
Is Internet Access a Human Right Debate Discussion |

|
I understand how crucial the topic of internet access as a human right is in our digital age. As someone who delved into this issue, I'm here to help you navigate the debate. This article will explore both sides of the argument and provide the insigh...
Author: Newton Waweru |
|
|
|
|
9
|
How is Identity Theft Committed Technology |

|
Navigating the complex world of identity theft and technology can be daunting. Rest assured, I've thoroughly explored this landscape, and I'm here to guide you. This article unpacks how criminals exploit technology to commit identity theft, ensuring ...
Author: Newton Waweru |
|
|
|
|
10
|
Cyber Espionage and Information Warfare Threats to National Security |

|
Cyber Espionage & Information Warfare can be daunting, but don't worry - we're here to help. As someone who's delved into this complex topic, I empathize with your need for guidance. This article offers clear, human insights into the critical aspects...
Author: Newton Waweru |
|
|
|
|
11
|
The History of Cybersecurity and Hacking A Detailed Guide |

|
I understand your interest in the history of cybersecurity and hacking, as it's a fascinating subject. Rest assured, I've delved deeply into the topic and will guide you. This article will explore key milestones and developments that shaped this ever...
Author: Newton Waweru |
|
|
|
|
12
|
The Danger of Mixing Cyberwarfare with Cyber Espionage |

|
Are you concerned about the potential hazards of combining cyber warfare and cyber espionage? You're not alone. As someone who has delved deep into this critical issue, I understand your concerns and am here to help. This article will explore the ris...
Author: Newton Waweru |
|
|
|
|
13
|
Can Binary Code Be Used for Hacking? Uncover the Truth |

|
Are you eager to learn about the possibilities of using binary code for hacking? My comprehensive article explores the reality of binary code's capabilities in the realm of hacking.
In general, binary code can be applied as a technique in the field ...
Author: Newton Waweru |
|
|
|
|
14
|
How To Check RAM Specifications in Your Computer |

|
Your computer serves its intended purpose when it has the capability. One of the most significant aspects of a computer is its RAM. The Ram of a computer is what determines how the computer performs.
Before purchasing any computer, you need to hav...
Author: James Fleming |
|
|
|
|
15
|
Tracking a Wi-Fi Password on Your Windows PC or Android Phone |

|
We need to have internet access to our devices, mostly smartphones and computers, to enjoy using them fully. This enables you to browse freely and interact with your friends on social media worldwide. One of the best ways to access the internet is ...
Author: James Fleming |
|
|
|
|
16
|
What Are Your Strategies To Avoid Being A Victim Of Cybercrime? |

|
Cybercrimes have been on the increase, with many unaware victims. When we hear about cybercrimes, we automatically think about hackers. But cybercrime is not just about hacking. It goes beyond that. Many people today use their devices, such as phones...
Author: James Fleming |
|
|
|
|
17
|
Things You Should Know Before Buying a Smart Home Device |

|
Do you want to be able to control your lights and appliances from your phone? Or maybe you're looking for a more efficient way to heat and cool your home. If so, then you may be considering purchasing a smart home device.
There are some things you s...
Author: Faith Cheruiyot |
|
|
|
|
18
|
How Can I Hack Someone's Wireless Network? |

|
Wireless networks or Wi-Fi are usually accessible to everyone who is within the transmission radius. You can use the hotspots in public places like restaurants, airports, parks, etc. This makes them more vulnerable to cyber-attacks. In fact, cracking...
Author: Tithi Raha |
|
|
|
|
19
|
What Android Repair Experts/Technician Want You to Know |

|
When it comes to android repair, with many guides on social media, many people think it's a do-it-yourself task, forgetting they need expert services and advice. It would be great to learn more about android repair from an expert's perspective. This ...
Author: Nancy Museo |
|
|
|
|
20
|
Game Console Repair Budget? Terrible Ways to Spend Your Money |

|
How much would you want to spend on a game repair service? Well, you are not sure. This article informs you on the terrible ways you can spend your money when you are getting game console repair services.
There are four ways you can avoid unnecessa...
Author: Caroline Chebet |
|
|
|
|
21
|
Bluetooth hacks: How to hack a car's Bluetooth? |

|
Bluetooth hacking is one of the most familiar hacks that hackers use. If you are a car owner, you must take precautions to keep your car safe from hackers. I want to keep myself and my car safe; that's why I researched and wrote this article to guide...
Author: Janet Kathalu |
|
|
|
|
22
|
Beginner Guide: How to Become an Ethical Hacker |

|
Dreaming to become an ethical hacker is one thing and becoming one in another one. It is not an easy ride in the park. The challenges and rough rides are part of the ethical hacker's journey. Allow me to take you the best ways to become an ethical ha...
Author: Berts Njoroge |
|
|
|
|
23
|
Password Security: How to Create a Strong Password (and Remember It) |

|
Have you ever typed a password and the system indicates that it is too weak or you add some symbols or numbers? As common as it is, a strong password saves you from intrusions and cyber attacks. It's hard to create a strong and memorable password wit...
Author: Fay Kokri |
|
|
|
|
24
|
What things can you do on the dark web? |

|
Have you always wondered what goes on in the dark web? I understand your curiosity, and I am here to break down all you need to know about the dark. Anything in darkness will be brought to light, literally.
There are a lot of activities that happen...
Author: Berts Njoroge |
|
|
|
|
25
|
How to Check If an Email Is Legit? |

|
“Phishing” is a popular term among hackers and hacking sites. These phishing emails are sent with the primary purpose of stealing valuable information or taking control of your networks.
It’s reported that every day nearly 3.4 billion phishing emai...
Author: Tithi Raha |
|
|
|
|
26
|
Why Do We Need Ethics for Internet Users? |

|
With the introduction of computers globally in the 1990s, the entire approach of working, communicating, and storing important information has changed. I mean, who would have thought that a machine can make one convey a message at any corner of the w...
Author: Collins Okoth |
|
|
|
|
27
|
What Are the Signs a Website Has Been Hacked? |
|
If you own a business, you likely depend a lot on your website. From eCommerce to marketing, your website is the backbone of your transactions and everything in between. Without its help, you could face a lot of setbacks. Nevertheless, many business...
Author: Ian Musyoka |
|
|
|
|
28
|
What Happens When a Site I Use Gets Hacked? |

|
In the Internet’s virtual world, security is very confusing as compared to the real world. Security is messy; difficult to develop and sustain. As much as the Internet is built around a system of protocols, these rules can often be ignored.
When...
Author: Ian Musyoka |
|
|
|