|
1
|
How have Online Scams Evolved Cybersecurity and Digital Deception |

|
Understanding the evolution of online scams is essential in this digital age. As someone who has thoroughly studied this issue, I share your concerns about this complex and ever-changing problem. This article is here to help, presenting a detailed lo...
Author: Newton Waweru |
|
|
|
|
2
|
Common Misconceptions about Cybersecurity |

|
It seems like you're curious about common misconceptions surrounding cybersecurity. Don't worry. I'm here to help you navigate this topic. As someone who has researched this extensively, this article will shed light on the most prevalent misunderstan...
Author: Newton Waweru |
|
|
|
|
3
|
What Is the Importance of Having a Strong Password Digital Protection |

|
Navigating the digital world, you may often wonder, "Why are strong passwords so crucial?" Passwords are your digital keys, guarding personal information and online identities. In this article, we'll delve into the importance of robust passwords to ...
Author: Newton Waweru |
|
|
|
|
4
|
How Do Authentication Processes Work Decoding Security |

|
Hello there! The mechanics of digital authentication might seem complex. This is a vast topic, but I'm here to clarify it with my deep understanding. This article will delve into the functioning of authentication processes.
Authentication processes ...
Author: Newton Waweru |
|
|
|
|
5
|
Why Should You Avoid Public Wifi Protecting Your Online Privacy |

|
Navigating the web safely is more crucial than ever. You might wonder, "What's the harm in using public Wi-Fi?" This article will explore why avoiding public Wi-Fi can significantly enhance online security. Let's delve into the risks and precautions ...
Author: Newton Waweru |
|
|
|
|
6
|
What are the Types of Cyber Security Types and Threats Defined |

|
Navigating the complex world of cyber security can be challenging, and we understand that. This article is a comprehensive exploration of the various types of cyber security, carefully crafted to equip you with the knowledge to secure your digital li...
Author: Newton Waweru |
|
|
|
|
7
|
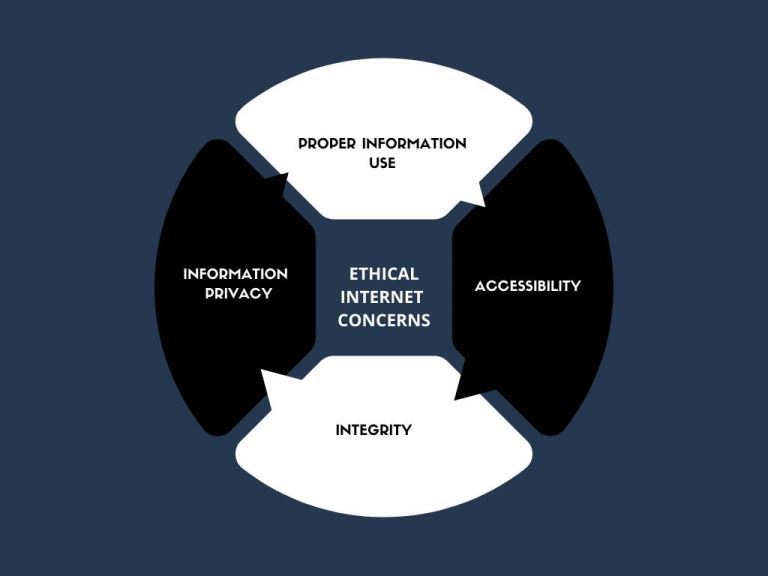
The Range and Scope of Internet Ethics A Comprehensive Guide |

|
Diving into the complex world of Internet Ethics? You're not alone! I've explored the range and scope of this topic to help you navigate these ethical dilemmas. This article will provide insights and guidance, ensuring you make informed decisions onl...
Author: Newton Waweru |
|
|
|
|
8
|
What are the 10 Commandments of Computer Ethics |

|
Navigating the digital world with respect and integrity is essential. As an expert in computer ethics, I've delved into the 10 Commandments of Computer Ethics, the cornerstone of responsible digital behavior. This article aims to help you better und...
Author: Newton Waweru |
|
|
|
|
9
|
What is a Possible Effect of Malicious Code |

|
Navigating the digital world can feel like a labyrinth, especially when malicious code lurks in the shadows. It's alarming, I know. But fear not; I've delved into this complex issue to help guide you. In this article, we'll illuminate the potential e...
Author: Newton Waweru |
|
|
|
|
10
|
The Biggest Cybersecurity Attacks Recorded |

|
Curious about the world of cybersecurity? To keep you informed, I have delved into the most massive cyber attacks ever recorded. Let's explore the critical incidents, their impact, and ways to stay protected together. By the end of this article, you'...
Author: Newton Waweru |
|
|
|
|
11
|
What is the Importance of Internet Ethics Responsible Online Behavior |

|
Navigating the digital world, internet ethics is a vital topic you're not alone in exploring. I've got you covered. I empathize with your quest for guidance, and in this article, I'll discuss the importance of ethical conduct online, privacy, and sec...
Author: Newton Waweru |
|
|
|
|
12
|
How Does Biometrics Change the Face of Security Enhancing Security |

|
Navigating the world of security can seem like a daunting task. With new technologies like biometrics rising, feeling curious and overwhelmed is normal. This article will guide you through how does biometrics change the face of security, providing in...
Author: Newton Waweru |
|
|
|
|
13
|
How is Identity Theft Committed Technology |

|
Navigating the complex world of identity theft and technology can be daunting. Rest assured, I've thoroughly explored this landscape, and I'm here to guide you. This article unpacks how criminals exploit technology to commit identity theft, ensuring ...
Author: Newton Waweru |
|
|
|
|
14
|
Things Every Employee Should Know about Cybersecurity Safety Tips |

|
Struggling with cybersecurity at work? You're not alone. As an employee, it's crucial to understand the basics of online safety. I've delved into the topic and can help you navigate this complex world. In this article, I'll explore key cybersecurity ...
Author: Newton Waweru |
|
|
|
|
15
|
My Account Has Been Hacked What Do I Do Secure Your Information |

|
Facing a hacked account can be a nightmare, and I understand your anxiety. Rest assured, I've delved deep into this issue and am here to help! This article will empathetically walk you through the essential steps to regain control and secure your acc...
Author: Newton Waweru |
|
|
|
|
16
|
What Are Your Strategies To Avoid Being A Victim Of Cybercrime? |

|
Cybercrimes have been on the increase, with many unaware victims. When we hear about cybercrimes, we automatically think about hackers. But cybercrime is not just about hacking. It goes beyond that. Many people today use their devices, such as phones...
Author: James Fleming |
|
|
|
|
17
|
How To Protect Yourself in an Internet Security Breach |

|
Since the advent of the Internet, online security has been a concern for both individuals and businesses. Unfortunately, despite our best efforts, cyberattacks continue to occur with alarming frequency.
There are several things you can do to safegu...
Author: Faith Cheruiyot |
|
|
|
|
18
|
Cyberstalking and How to Protect Yourself From Identity Theft |

|
Image: Internet Security
Creating a better online experience in the data and communication field has become a non-negotiable topic. Given the current move into the digital space, advanced data platforms and new communication channels have been cre...
Author: Ian Musyoka |
|
|
|
|
19
|
What Are Ethical and Unethical Practices Related to Internet Use? |
|
Information technology has made the world more accessible than ever in history. Different people from different parts of the world have the ability to access the internet and simultaneously make use of online resources. Do not be deceived that what...
Author: Ian Musyoka |
|
|
|
|
20
|
Why Do We Need Ethics for Internet Users? |

|
With the introduction of computers globally in the 1990s, the entire approach of working, communicating, and storing important information has changed. I mean, who would have thought that a machine can make one convey a message at any corner of the w...
Author: Collins Okoth |
|
|
|
|
21
|
What Happens When a Site I Use Gets Hacked? |

|
In the Internet’s virtual world, security is very confusing as compared to the real world. Security is messy; difficult to develop and sustain. As much as the Internet is built around a system of protocols, these rules can often be ignored.
When...
Author: Ian Musyoka |
|
|
|