|
1
|
How have Online Scams Evolved Cybersecurity and Digital Deception |

|
Understanding the evolution of online scams is essential in this digital age. As someone who has thoroughly studied this issue, I share your concerns about this complex and ever-changing problem. This article is here to help, presenting a detailed lo...
Author: Newton Waweru |
|
|
|
|
2
|
Emerging Trends and Challenges in Cybersecurity |

|
In today's rapidly evolving digital landscape, emerging trends and challenges in cybersecurity are of great concern. Together, we'll explore these trends and challenges, arming you with the knowledge to protect your digital assets. This article will ...
Author: Newton Waweru |
|
|
|
|
3
|
What are the Challenges Faced in Cybersecurity Risks and Solutions |

|
Cybersecurity is a growing concern, and navigating its challenges can be daunting. You're not alone in seeking help; I'm here to provide the guidance you need. This article dives into the key obstacles faced in cybersecurity, offering practical insig...
Author: Newton Waweru |
|
|
|
|
4
|
The Range and Scope of Internet Ethics A Comprehensive Guide |

|
Diving into the complex world of Internet Ethics? You're not alone! I've explored the range and scope of this topic to help you navigate these ethical dilemmas. This article will provide insights and guidance, ensuring you make informed decisions onl...
Author: Newton Waweru |
|
|
|
|
5
|
The Biggest Cybersecurity Attacks Recorded |

|
Curious about the world of cybersecurity? To keep you informed, I have delved into the most massive cyber attacks ever recorded. Let's explore the critical incidents, their impact, and ways to stay protected together. By the end of this article, you'...
Author: Newton Waweru |
|
|
|
|
6
|
Cyber Espionage and Information Warfare Threats to National Security |

|
Cyber Espionage & Information Warfare can be daunting, but don't worry - we're here to help. As someone who's delved into this complex topic, I empathize with your need for guidance. This article offers clear, human insights into the critical aspects...
Author: Newton Waweru |
|
|
|
|
7
|
The History of Cybersecurity and Hacking A Detailed Guide |

|
I understand your interest in the history of cybersecurity and hacking, as it's a fascinating subject. Rest assured, I've delved deeply into the topic and will guide you. This article will explore key milestones and developments that shaped this ever...
Author: Newton Waweru |
|
|
|
|
8
|
The Danger of Mixing Cyberwarfare with Cyber Espionage |

|
Are you concerned about the potential hazards of combining cyber warfare and cyber espionage? You're not alone. As someone who has delved deep into this critical issue, I understand your concerns and am here to help. This article will explore the ris...
Author: Newton Waweru |
|
|
|
|
9
|
How to Protect Your Company Against Cyber Espionage |

|
Concerned about cyber espionage threatening your business? You're not alone. As an experienced researcher, I understand the need to stay vigilant. In this article, I'll explore practical steps to safeguard your company, providing you with the tools t...
Author: Newton Waweru |
|
|
|
|
10
|
Where Will Cyber Security be 10 Years from Now Navigating the Future |

|
As we navigate an increasingly digital world, you might wonder where cyber security will be in 10 years. After researching extensively, I'm confident in sharing valuable insights. This article will explore future cyber security trends and challenges...
Author: Newton Waweru |
|
|
|
|
11
|
The Next Big Thing in Cyber Security Discover Innovative Solutions |

|
Ready to uncover the Next Big Thing in Cyber Security? You're not alone! As cyber threats evolve, so should our defenses. Fear not, I've delved deep into this crucial issue to help you stay informed and prepared. Join me in this article as we explore...
Author: Newton Waweru |
|
|
|
|
12
|
What Are the Five Pillars of Cloud Security |

|
Addressing the security challenges in cloud computing requires an understanding of the pillars. A company needs insight into shared responsibility in managing data, privileges, users, and resources. Cloud security requires frameworks to ensure all po...
Author: Eunice Njuguna |
|
|
|
|
13
|
Why Are Binary Numbers Used in Electronics? |

|
Discover the fascinating world of electronics. Ever curious about the significance of binary numbers in this industry? This article will uncover the key role of binary in electronics and examine its use for data communication and processing. Get read...
Author: Newton Waweru |
|
|
|
|
14
|
Why Was Binary Code Invented? Discover the History of Binary Code |

|
Discover the origin of binary code in this informative article. Have you ever wondered why binary code was invented and how it has revolutionized the way we process and store data?
As a whole, the invention of binary code was born as a solution for ...
Author: Newton Waweru |
|
|
|
|
15
|
Binary Code vs. Source Code [Know the Difference] |

|
In this article, we'll delve into the differences between binary code and source code and provide examples to assist in understanding the usage and application of each in the realm of computer programming. Whether you're a beginner or an experienced ...
Author: Newton Waweru |
|
|
|
|
16
|
Can Binary Code Be Used for Hacking? Uncover the Truth |

|
Are you eager to learn about the possibilities of using binary code for hacking? My comprehensive article explores the reality of binary code's capabilities in the realm of hacking.
In general, binary code can be applied as a technique in the field ...
Author: Newton Waweru |
|
|
|
|
17
|
Binary code vs. Hexadecimal [A Guide to Understand the Differences] |

|
Are you struggling to understand the differences between Binary and Hexadecimal code? This comprehensive guide breaks down the complex concepts into easy-to-understand terms.
As a whole, Binary code and Hexadecimal are two methods of representing i...
Author: Newton Waweru |
|
|
|
|
18
|
What is Binary Code Used For? Learn Its Applications and Uses |

|
Explore the use of binary code and its implications in the current technology through this enlightening piece. If you're intrigued by the role of binary code in modern devices, you've arrived at the ideal destination.
As a whole, the binary system i...
Author: Newton Waweru |
|
|
|
|
19
|
Who Invented Binary Code? The Father of Binary Code |

|
George Boole is believed to be the "Father of Binary Code." Are you interested in knowing more about him? In that case, you have arrived at the correct location. I can answer any questions you may have about George Boole's life and legacy.
George B...
Author: Newton Waweru |
|
|
|
|
20
|
What You Need to Know Concerning the Latest Apple iOS Cheat Sheets |

|
What You Need to Know Concerning the Latest Apple iOS Cheat Sheets
Every mobile user wants a phone that works correctly and per their expectations. Every brand has different operating systems that improve phones' performance. For example, iPhone, iP...
Author: James Fleming |
|
|
|
|
21
|
Deciphering the World of Computer Acronyms: A Must-Know List |
|
Deciphering the World of Computer Acronyms: A Must-Know List
As technology continues to advance and evolve, it can be overwhelming to keep up with all the diff erent acronyms thrown around in the world of computers. There are so many other terms and...
Author: James Fleming |
|
|
|
|
22
|
Things You Didn't Know About Backup Services [What Are They?] |

|
A good backup service is crucial for ensuring all your data is safe from hardware failure or accidental deletion. Backup services offer companies and individuals the protection they need to keep their data safe. With backup services, companies can co...
Author: Faith Cheruiyot |
|
|
|
|
23
|
What Terms Everyone in the Game Console Repair Industry Should Know? |

|
The terms used in gaming consoles and their repair can be intimidating, but this guide explains them in simple terms.
On average, there are hundreds of terms used in games and consoles. The common ones include baking, badge, a bonus stage, AAA, AL,...
Author: Caroline Chebet |
|
|
|
|
24
|
Computer Numbers: How Computers Generate Random Numbers |

|
Computer random numbers is a complex topic. It consists of 'yeses' and 'nos'. For a couple of years, I have been studying numbers and I am hereby crafting a well-simplified article to make you understand how computers generate random numbers. So, let...
Author: Berts Njoroge |
|
|
|
|
25
|
Beginner Guide: How to Become an Ethical Hacker |

|
Dreaming to become an ethical hacker is one thing and becoming one in another one. It is not an easy ride in the park. The challenges and rough rides are part of the ethical hacker's journey. Allow me to take you the best ways to become an ethical ha...
Author: Berts Njoroge |
|
|
|
|
26
|
What Is Overclocking? Beginner's Guide to Speeding up PCs |

|
Overclocking is essentially an act of manually increasing the clock speeds of the CPU, RAM, or GPU. It is common among computer geeks, IT professionals, and heavy computer users like Gamers interested in maximizing their processor's potential. To suc...
Author: Collins Okoth |
|
|
|
|
27
|
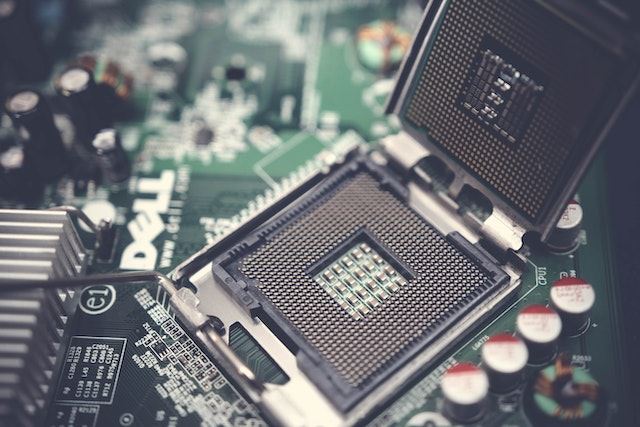
How computers work: why is the processor important? |

|
We have prepared this article with the sole aim of informing you what a processor is, it's components and how they function together in transforming data and instructions into useful information.
,
A CPU or processor is an electronic circuit found ...
Author: Gloria Mutuku |
|
|
|
|
28
|
What is the Internet of Things IoT |

|
The Internet of things (IoT) is a general term for the increasing number of electronics that are not conventional computer equipment but connected to the Internet to send information, receive instructions, or both.
Tech analyst company IDC forecasts...
Author: Collins Okoth |
|
|
|
|
29
|
Quantum Computers Explained Simply |

|
In the 1930s, Alan Turing developed the Turing machine. This machine comprises an unlimited length of tape that was subdivided into small squares. Each one of these little squares could either store a 1 or a 0 or be left blank. Consequently, a read a...
Author: Collins Okoth |
|
|
|