|
1
|
How Does TwoFactor Authentication 2FA Work |

|
Navigating online security can seem like a maze. I'm here to guide you through it. Let's explore the world of two-factor authentication (2FA), a vital tool for protecting your data. I've delved deep into this topic and promise to break it down in a w...
Author: Newton Waweru |
|
|
|
|
2
|
How Does Biometrics Change the Face of Security Enhancing Security |

|
Navigating the world of security can seem like a daunting task. With new technologies like biometrics rising, feeling curious and overwhelmed is normal. This article will guide you through how does biometrics change the face of security, providing in...
Author: Newton Waweru |
|
|
|
|
3
|
How is Identity Theft Committed Technology |

|
Navigating the complex world of identity theft and technology can be daunting. Rest assured, I've thoroughly explored this landscape, and I'm here to guide you. This article unpacks how criminals exploit technology to commit identity theft, ensuring ...
Author: Newton Waweru |
|
|
|
|
4
|
Understanding SSID: What Is It and How Does It Work? |

|
Understanding SSID: What Is It and How Does It Work?
Wireless networks have become increasingly popular, enabling people to connect to the Internet and access network resources without the need for wired connections. One of the key components of wir...
Author: James Fleming |
|
|
|
|
5
|
How to Detect Hidden Surveillance Cameras With Your Phone |

|
How to Detect Hidden Surveillance Cameras With Your Phone
Have you ever suspected that you were being watched but couldn't find any visible surveillance cameras? It's possible that the camera or cameras were hidden, making it difficult to detect the...
Author: James Fleming |
|
|
|
|
6
|
Controlling and Viewing devices connected to your Wi-Fi Network |

|
It's worth taking the time to see who is connected to your Wi-Fi network. Your home network security could be compromised if unauthorized users are piggybacking on your connection, slowing down your speeds and using up your data - all without you k...
Author: James Fleming |
|
|
|
|
7
|
What Is An Example of Smart Home Automation? |

|
When it comes to the future of the home, many people think of smart homes. A smart home is a residence equipped with advanced automation features, making it more intelligent and efficient.
There are many different types of smart home automation, so...
Author: Faith Cheruiyot |
|
|
|
|
8
|
Smart Security System: Protecting Your Home From Burglars |

|
Like most people, you probably think of your home as your sanctuary. It's where you feel safe and secure, and it's a refuge from the hustle and bustle of the outside world. But what happens when a burglary shatters that sense of safety? A smart secur...
Author: Faith Cheruiyot |
|
|
|
|
9
|
Why is My Ping So High All Of a Sudden? Check Out The Reasons! |

|
Ping latency is a crucial thing to maintain especially when it comes to gaming that requires fast responsiveness from your end. For any online gaming, you need a lower ping to better experience everything. High ping can negatively alter the gaming ex...
Author: Tithi Raha |
|
|
|
|
10
|
What Does a Virus Scan Actually Do: A Definitive Guide |

|
A virus scan runs through a computer system to check malicious threats and remove them. There are two types of protection provided by antivirus software during a virus scan. This includes proactive and reactive protection. The former spots potential ...
Author: Tithi Raha |
|
|
|
|
11
|
Beginner Guide: How to Become an Ethical Hacker |

|
Dreaming to become an ethical hacker is one thing and becoming one in another one. It is not an easy ride in the park. The challenges and rough rides are part of the ethical hacker's journey. Allow me to take you the best ways to become an ethical ha...
Author: Berts Njoroge |
|
|
|
|
12
|
Computer Repair: How to Detect Crypto Mining Malware |

|
The vast growth of the cryptocurrency market has been something to marvel at over the past few years. However, the concept of anonymous payouts has given cybercriminals a reason to be part of the game. They have developed crypto-mining malware that c...
Author: Ian Musyoka |
|
|
|
|
13
|
What Happens When a Site I Use Gets Hacked? |

|
In the Internet’s virtual world, security is very confusing as compared to the real world. Security is messy; difficult to develop and sustain. As much as the Internet is built around a system of protocols, these rules can often be ignored.
When...
Author: Ian Musyoka |
|
|
|
|
14
|
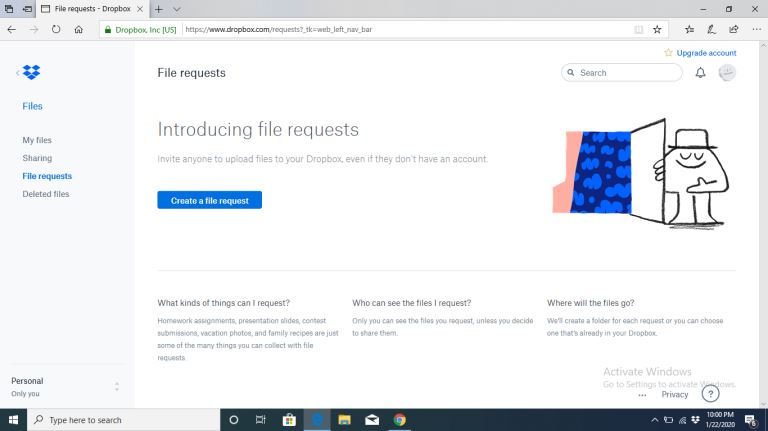
How Does Cloud Sharing Work |
|
Whether you are a business dealing with loads of information or an individual saving personal files, data is an integral part of day-to-day activities. Handling data is a standard process, and as you collect, save, and share information, it is essent...
Author: Eunice Njuguna |
|
|
|
|
15
|
What's Wrong With Using Public Wi-Fi? |

|
Picture yourself in your favorite cafe, drinking a hot cup of coffee while taking advantage of the free Wi-Fi to update your feed or keep up with the news. I bet that to some of us, and this already sounds like a very familiar setting. However, did...
Author: Ian Musyoka |
|
|
|
|
16
|
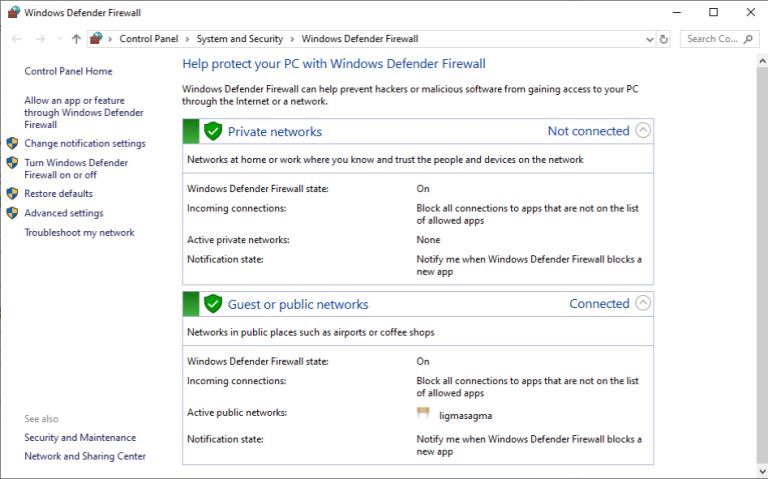
What Does a Firewall Do? |
|
Before I started writing this, I thought to myself, “Who really needs a firewall?” But, as it turns out, most of us do. If your personal or company computer is connected to the internet, your network is always exposed to threats and risks. This mea...
Author: Ian Musyoka |
|
|
|