|
1
|
Can Computer Repair Shops Steal Your Data How to Prevent Them |

|
Regardless of the type of laptop or computer you use, it'll cause you some trouble at some point. Because technical issues may arise with your devices. In that case, you have to take your system to a repair shop for further help. But, a lot of people...
Author: Tithi Raha |
|
|
|
|
2
|
What is The Difference Between Computer Repair Technicians & Help Desk |

|
When it comes to the help desk analyst and computer repair Topeka, KS technician, people often need clarification on these two. Regardless of how similar these two sound, they have significant differences. However, both of them are designed to help c...
Author: Tithi Raha |
|
|
|
|
3
|
Characteristics of a Good Computer Repair Technician in Topeka, KS |

|
Professional technicians for Computer Repair in Topeka, Kansas are certainly responsible for maintaining, testing, and installing computer networks as well as software. However, these aren't the only skills required to succeed in this field. A techni...
Author: Tithi Raha |
|
|
|
|
4
|
What Is Binary Also Known As? Discover the Different Names for Binary |

|
Uncover the secret of binary and its various names. Delve into the unique labels used to describe binary thoroughly. Embark on an enlightening journey to grasp this concept effortlessly with simple yet comprehensive information. Rely on my extensive ...
Author: Newton Waweru |
|
|
|
|
5
|
How Do Computers Recognize Digital Signals? |

|
How do computers translate digital signals? Have you ever wondered how computers can understand and respond to digital signals? My comprehensive article delves deep into the technicalities and highlights the essential components that make computer re...
Author: Newton Waweru |
|
|
|
|
6
|
What Makes the Binary System Applicable to Computer Circuits? |

|
Discover the importance of the binary system in computer circuits. Are you eager to understand the inner workings of computers and the significance of the binary system?
The most important reason that makes the binary system applicable to Computer ...
Author: Newton Waweru |
|
|
|
|
7
|
Why Was Binary Code Invented? Discover the History of Binary Code |

|
Discover the origin of binary code in this informative article. Have you ever wondered why binary code was invented and how it has revolutionized the way we process and store data?
As a whole, the invention of binary code was born as a solution for ...
Author: Newton Waweru |
|
|
|
|
8
|
Binary code VS ASCII [Understanding the Differences] |

|
This piece delves into the differences between binary and ASCII coding methodologies. If you're seeking information and a thorough examination of these coding techniques, your search has come to an end. I understand the confusion that comes with comp...
Author: Newton Waweru |
|
|
|
|
9
|
How to force quit on a mac |

|
How to force quit on a mac
Have you ever felt like smashing your computer into a million pieces just because an app misbehaves and is not responsive? Well, I am sure we all have been there once or twice. Therefore, instead of bashing your expensive ...
Author: James Fleming |
|
|
|
|
10
|
The Top 5 Best Drawing and Animation laptops Under 1000 Dollars |

|
The Top 5 Best Drawing and Animation laptops Under 1000 Dollars
When choosing the best drawing and animation laptop, there are crucial factors to consider for effective work results. These activities are intensive and require a computer with a quick...
Author: James Fleming |
|
|
|
|
11
|
Why Do Games Download Slow On PC? Check Out The Solution! |

|
Sometimes you will notice that your computer is downloading files at an extremely poor speed. Whether it could be your ISP or faulty hardware of your PC, connection interruption can be quite frustrating. If you've to wait for the entire day just to d...
Author: Tithi Raha |
|
|
|
|
12
|
Network Setup Tutorial - How to Set up a VPN Connection |

|
A VPN can add an extra layer of security and privacy. It helps you hide your identity so you can browse the internet safely and anonymously. The best thing is that you don't need to be a tech expert to set up your VPN.
There are many ways to set up...
Author: Faith Cheruiyot |
|
|
|
|
13
|
Mac Repair Tips & Tricks That You Need To Know |

|
Mac operating system is reliable and famous among its users. Many people switch from other operating systems like Windows and Linux and would like to learn how to troubleshoot and fix any issues that come along the way.
There are many mac repair ti...
Author: Faith Cheruiyot |
|
|
|
|
14
|
What Are The Dos And Don'ts In Custom PC Build? |

|
Aspiring to build your PC or hire an expert? For perfect custom PC build needs a proper understanding of dos and don'ts when building a PC.
There are plenty of ways to teach you how to build your PC, for example, through videos. Building the PC lets...
Author: Faith Cheruiyot |
|
|
|
|
15
|
Computer Tune Advice: How To Get Rid Of Viruses On Your Computer |

|
Computer viruses come in different ways and forms. It consists of code designed to interrupt the normal functioning of the computer and invade the computer system, software, and files. Most of them are harmful, and you need to protect your computer f...
Author: Faith Cheruiyot |
|
|
|
|
16
|
What Are The Modern Rules of Backup Services? |

|
Did you know there are modern rules for backup services? Backing up data is vital to maintain computer function and avoid data loss.
There are many rules in the backup services, including always backing up your data, automating your backups, and con...
Author: Faith Cheruiyot |
|
|
|
|
17
|
10 Undeniable Benefits of Remote Assistance |

|
Advancements in technology have led to several changes in how we live and work. One of the most significant changes has been the rise of remote working. With the ability to connect to the internet from anywhere in the world, more and more people are ...
Author: Faith Cheruiyot |
|
|
|
|
18
|
How to Fix Your Cellphone or Tablet Remotely |

|
Have you ever been in the middle of watching your favorite show on your tablet, only to have the battery dead? Or maybe you were playing a game on your phone, and suddenly the screen went blank. If you're like most people, your first instinct is to p...
Author: Faith Cheruiyot |
|
|
|
|
19
|
How To Protect Yourself in an Internet Security Breach |

|
Since the advent of the Internet, online security has been a concern for both individuals and businesses. Unfortunately, despite our best efforts, cyberattacks continue to occur with alarming frequency.
There are several things you can do to safegu...
Author: Faith Cheruiyot |
|
|
|
|
20
|
Network Setup Tutorial - Configuring a Remote Access Server |

|
Many offices have many users and teams with multiple branches. Using remote access servers enables businesses and organizations to let their staff access all the devices remotely. It mainly works in areas where the users cannot access the local area ...
Author: Faith Cheruiyot |
|
|
|
|
21
|
What is the Best Software for Making Video Tutorials? |

|
Are you planning to make video tutorials? Do you want to explain how your products and services function using the software? Video Tutorial software is ideal as it lets you edit, generate, manipulate and enhance videos. Such ensures the corporate and...
Author: Faith Cheruiyot |
|
|
|
|
22
|
How To Turn off Touch Screen on Promethean Board |

|
After using the Promethean board in your class or lecture room to conduct different activities like drawing, annotation, and writing. You get confused about how to turn it off after its usage. Many may see you as an expert when you know to turn off t...
Author: Berts Njoroge |
|
|
|
|
23
|
How Do You Find Your Router's IP Address? |

|
Without knowing your router's IP address, you can't make any changes to it. Whether you want to create a new password for your Wi-Fi, change the name of your network, or switch to a different channel for boosting your connection, an IP address is a m...
Author: Tithi Raha |
|
|
|
|
24
|
How Does a Computer Work: A Definitive Guide |

|
A computer is an electronic machine that acts as an information processor. It takes the raw information or data, stores it, works on it, and spits the result out. However, there is an entire process behind how the computer works.
A computer is desi...
Author: Tithi Raha |
|
|
|
|
25
|
How computers work: why is the processor important? |

|
We have prepared this article with the sole aim of informing you what a processor is, it's components and how they function together in transforming data and instructions into useful information.
,
A CPU or processor is an electronic circuit found ...
Author: Gloria Mutuku |
|
|
|
|
26
|
How to Play iPhone MOV Files on Windows 10? |

|
MOV is a default multimedia format of Apple for iPhones, Macs, and iPads used for storing audio and video content such as music and movies. The format was primarily developed for native playback on iPhones, iPads, and Mac computers. It includes singl...
Author: Tithi Raha |
|
|
|
|
27
|
How do I change the default destination for my downloads? |

|
The default destination for downloads on computers running Microsoft Windows Operating System (Windows 7, Windows 8, or Windows 10) is the C:/drive. The C:/drive is also the windows system drive where the operating system is located. For a computer ...
Author: Ujunwa Chibuzor |
|
|
|
|
28
|
Is my computer worth fixing? |

|
Constant computer breakdowns can be frustrating, and if you are a frequent visitor to the repair shop you might start thinking of buying a new computer. However, a computer technician can advise you on the condition of your machine and if it is likel...
Author: Gloria Mutuku |
|
|
|
|
29
|
Does private browsing actually work? |

|
With today's advanced technology, targeted ads and recommendation algorithms leave no space for privacy online. In line with this, you could expect your 'private' surfing through incognito mode to stay private, whereby you can remain anonymous. Howev...
Author: Collins Okoth |
|
|
|
|
30
|
How Do Search Engines Work? |

|
You’re in the kitchen making your mom’s favorite pizza. To get topping ideas, you open your web browser to perform a search. You type ‘topping ideas’ in the search box, hit ‘Enter,’ and get eighty-nine million results in about half a second. For th...
Author: Ian Musyoka |
|
|
|
|
31
|
How does Chromecast work technically? |

|
Chromecast is a small disc-shaped device from Google that plugs into the High-Definition Multimedia Interface (HDMI) port of your television. It streams content through the Wi-Fi connection of your mobile device or computer, from streaming services s...
Author: Ujunwa Chibuzor |
|
|
|
|
32
|
How to Check If an Email Is Legit? |

|
“Phishing” is a popular term among hackers and hacking sites. These phishing emails are sent with the primary purpose of stealing valuable information or taking control of your networks.
It’s reported that every day nearly 3.4 billion phishing emai...
Author: Tithi Raha |
|
|
|
|
33
|
Can My Employer Monitor My Work Computer At Home? |

|
An employer has every right to monitor the work computers of their employees at home. The employer will do so for various reasons: they will need to ensure their employees' productivity. It is also for the protection of the organization's software ...
Author: Gloria Mutuku |
|
|
|
|
34
|
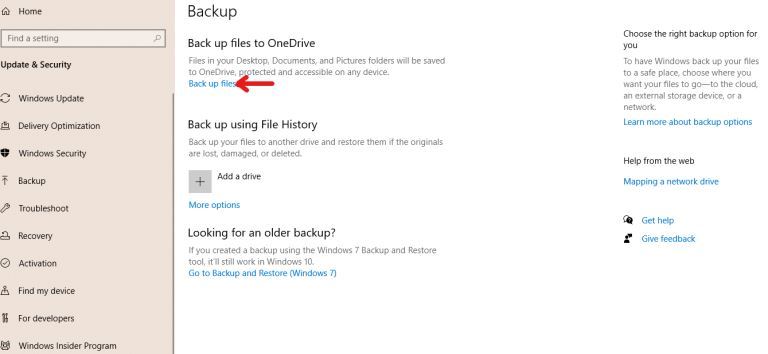
How to Backup Computer Windows 10? |
|
Backing up your computer windows 10 isn’t optional but a necessity.
The process starts by clicking on the “start” button on your Windows 10 system, navigating to the “setting” page, then to the “update & security” section, clicking on “backup,” and...
Author: Tithi Raha |
|
|
|
|
35
|
Why Do We Need Ethics for Internet Users? |

|
With the introduction of computers globally in the 1990s, the entire approach of working, communicating, and storing important information has changed. I mean, who would have thought that a machine can make one convey a message at any corner of the w...
Author: Collins Okoth |
|
|
|