|
1
|
What are the Challenges Faced in Cybersecurity Risks and Solutions |

|
Cybersecurity is a growing concern, and navigating its challenges can be daunting. You're not alone in seeking help; I'm here to provide the guidance you need. This article dives into the key obstacles faced in cybersecurity, offering practical insig...
Author: Newton Waweru |
|
|
|
|
2
|
What are the Types of Cyber Security Types and Threats Defined |

|
Navigating the complex world of cyber security can be challenging, and we understand that. This article is a comprehensive exploration of the various types of cyber security, carefully crafted to equip you with the knowledge to secure your digital li...
Author: Newton Waweru |
|
|
|
|
3
|
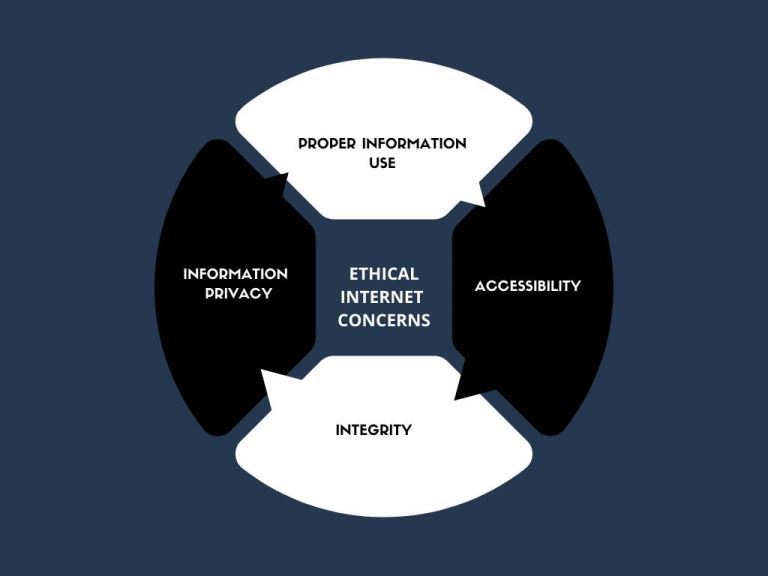
The Range and Scope of Internet Ethics A Comprehensive Guide |

|
Diving into the complex world of Internet Ethics? You're not alone! I've explored the range and scope of this topic to help you navigate these ethical dilemmas. This article will provide insights and guidance, ensuring you make informed decisions onl...
Author: Newton Waweru |
|
|
|
|
4
|
What are the 3 Main Pillars of Cybersecurity Internet Safety |

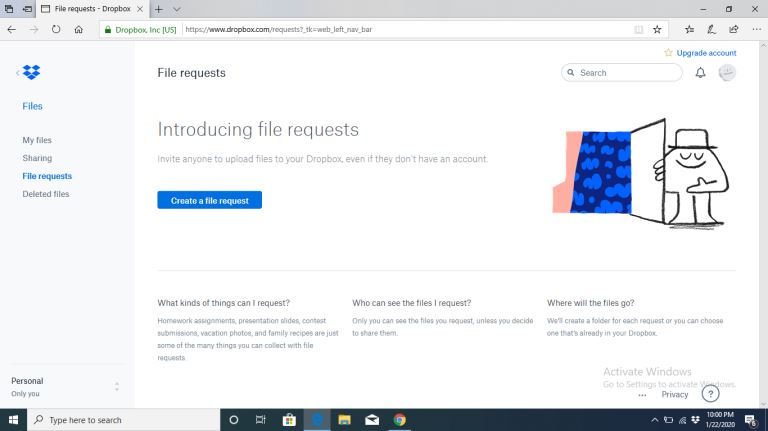
|
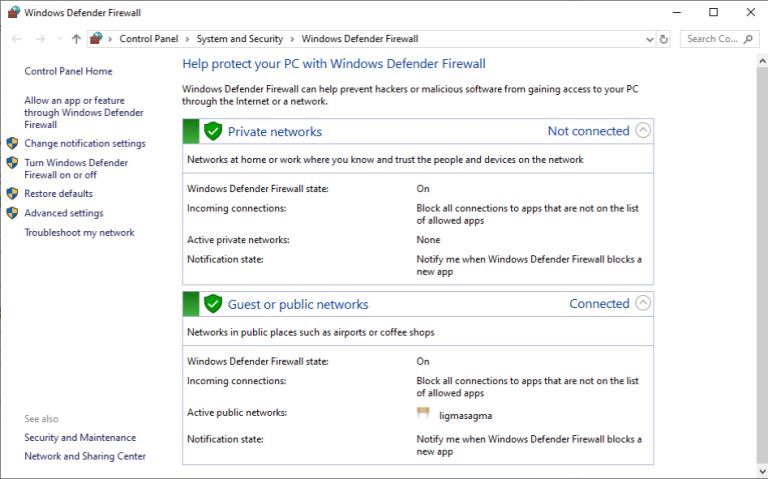
I understand cybersecurity can be complex and daunting, but don't worry - I'm here to help. As someone who has researched this topic extensively, I'll share the three main pillars of cybersecurity clearly and concisely, ensuring you gain a solid unde...
Author: Newton Waweru |
|
|
|
|
5
|
Cyber Espionage and Information Warfare Threats to National Security |

|
Cyber Espionage & Information Warfare can be daunting, but don't worry - we're here to help. As someone who's delved into this complex topic, I empathize with your need for guidance. This article offers clear, human insights into the critical aspects...
Author: Newton Waweru |
|
|
|
|
6
|
Methods that Employees Can Expose Company Data Accidentally |

|
Concerned about employees accidentally exposing company data? You're not alone. I've delved into this issue, and I'm here to help. In this article, I'll explore standard methods that can lead to unintentional data leaks so that you can take preventiv...
Author: Newton Waweru |
|
|
|
|
7
|
The Danger of Mixing Cyberwarfare with Cyber Espionage |

|
Are you concerned about the potential hazards of combining cyber warfare and cyber espionage? You're not alone. As someone who has delved deep into this critical issue, I understand your concerns and am here to help. This article will explore the ris...
Author: Newton Waweru |
|
|
|
|
8
|
How to Protect Your Company Against Cyber Espionage |

|
Concerned about cyber espionage threatening your business? You're not alone. As an experienced researcher, I understand the need to stay vigilant. In this article, I'll explore practical steps to safeguard your company, providing you with the tools t...
Author: Newton Waweru |
|
|
|
|
9
|
Things Every Employee Should Know about Cybersecurity Safety Tips |

|
Struggling with cybersecurity at work? You're not alone. As an employee, it's crucial to understand the basics of online safety. I've delved into the topic and can help you navigate this complex world. In this article, I'll explore key cybersecurity ...
Author: Newton Waweru |
|
|
|
|
10
|
The Next Big Thing in Cyber Security Discover Innovative Solutions |

|
Ready to uncover the Next Big Thing in Cyber Security? You're not alone! As cyber threats evolve, so should our defenses. Fear not, I've delved deep into this crucial issue to help you stay informed and prepared. Join me in this article as we explore...
Author: Newton Waweru |
|
|
|
|
11
|
My Account Has Been Hacked What Do I Do Secure Your Information |

|
Facing a hacked account can be a nightmare, and I understand your anxiety. Rest assured, I've delved deep into this issue and am here to help! This article will empathetically walk you through the essential steps to regain control and secure your acc...
Author: Newton Waweru |
|
|
|
|
12
|
What Are the Five Pillars of Cloud Security |

|
Addressing the security challenges in cloud computing requires an understanding of the pillars. A company needs insight into shared responsibility in managing data, privileges, users, and resources. Cloud security requires frameworks to ensure all po...
Author: Eunice Njuguna |
|
|
|
|
13
|
Can Computer Repair Shops Steal Your Data How to Prevent Them |

|
Regardless of the type of laptop or computer you use, it'll cause you some trouble at some point. Because technical issues may arise with your devices. In that case, you have to take your system to a repair shop for further help. But, a lot of people...
Author: Tithi Raha |
|
|
|
|
14
|
Can Computer Technicians Check Your History How to Prevent It |

|
It's pretty common that occasionally you may run into issues with your computer system. It may break down, malfunction, or be a victim of a ransomware attack. Regardless of the reasons, you're bound to call a repair technician. But, a lot of you doub...
Author: Tithi Raha |
|
|
|
|
15
|
What Security Parameters are Present in the Cloud? |

|
The security parameters present in the cloud are the technologies designed to counter internal and external threats. They include data loss prevention applications, disaster recovery tools, and identity access management systems. Most cloud security ...
Author: Eunice Njuguna |
|
|
|
|
16
|
Bluetooth 5 and Its Benefits: Why You Should Care |

|
Bluetooth 5 and Its Benefits: Why You Should Care
Bluetooth 5 is the evolution of the technology that updates and upgrades the previous Bluetooth 4.2 edition. It's not the most recent upgrade, but it's still good and offers multiple benefits over it...
Author: James Fleming |
|
|
|
|
17
|
6 Proven Ways to Remove Write Protection from USB in Windows 10 and Windows 11 |
|
6 Proven Ways to Remove Write Protection from USB in Windows 10 and Windows 11
How do you remove write protection from USB on Windows 10 or 11? Worry no more! With this simple guide, you can remove write protection from USB on a PC running the lates...
Author: James Fleming |
|
|
|
|
18
|
How do I remove write protection from my SanDisk? |

|
How do I remove write protection from my SanDisk?
While working on computers using external storage devices, they may be write-protected, which means that no operation can be done on them. A write-protected disk only allows the user to read data fro...
Author: James Fleming |
|
|
|
|
19
|
How Do You Identify The Cause And Fix Slow Download Speeds? |

|
A slow internet connection not only leaves everyone frustrated but also interrupts your work. Since there are so many problems that can cause the slowdown, it becomes difficult to identify the root cause of this disruption. However, you must find out...
Author: Tithi Raha |
|
|
|
|
20
|
Email Migration Tips: How Does Email Migration Work? |

|
Do you want to migrate your email from one host to another? In the email industry, migration can sometimes be risky and needs a lot of attention to avoid problems. Before starting, knowing what to expect from the email migration process will help you...
Author: Faith Cheruiyot |
|
|
|
|
21
|
iPod Repair Gone Wrong? Here's is What To Do |

|
If you're the owner of an iPod, then you know that it's not only a handy device to have for listening to your favorite music. But also for storing all sorts of other files. However, what do you do if something goes wrong with your iPod and needs repa...
Author: Faith Cheruiyot |
|
|
|
|
22
|
Facts About In-home Computer Service That Will Make You Laugh |

|
Modern life would be unimaginable without computers. From paying bills to managing our calendars, these devices play a major role in our day-to-day lives. So, when something goes wrong with our computer, it can be a real hassle.
There are many facts...
Author: Faith Cheruiyot |
|
|
|
|
23
|
What Are The Best Backup Services Strategies You Should Try? |

|
Are you aspiring to perform data recovery in your organization or want to hire someone? Before starting over, it is a wise idea that you understand the best backup services strategies.
There are several important backup services strategies users in ...
Author: Faith Cheruiyot |
|
|
|
|
24
|
10 Undeniable Benefits of Remote Assistance |

|
Advancements in technology have led to several changes in how we live and work. One of the most significant changes has been the rise of remote working. With the ability to connect to the internet from anywhere in the world, more and more people are ...
Author: Faith Cheruiyot |
|
|
|
|
25
|
Network Setup Tutorial - Configuring a Remote Access Server |

|
Many offices have many users and teams with multiple branches. Using remote access servers enables businesses and organizations to let their staff access all the devices remotely. It mainly works in areas where the users cannot access the local area ...
Author: Faith Cheruiyot |
|
|
|
|
26
|
How to Secure Your New Computer Against Viruses and Malware |

|
Do you have a new computer at home, at your workplace, or in your business? Are you worried that viruses and malware may attack your setup? You can use several ways to ensure that your new setup is safe from viruses and malware.
There are many cases...
Author: Caroline Chebet |
|
|
|
|
27
|
How to unlock computer screen Windows 11? |

|
Windows 11 has quite new features that are not in previous Windows versions. Learning how to do simple-to-complicated tasks is mandatory to have an excellent experience on Windows 11. One such task is unlocking Windows 11 screen. This article will di...
Author: Berts Njoroge |
|
|
|
|
28
|
How to Fix Windows Can't Format Flash Drive? |

|
The Windows can't format flash drive is a common error. It makes you waste time and can be a bad experience if you have no clue on how to go about it. It's even worse if you have no files backup. Luckily, I have all you need to know 'windows cant for...
Author: |
|
|
|
|
29
|
What Is a Burner Phone, and When Should You Use One |

|
I have been wondering how a burner phone can be used or if it is necessary to have one. I am sure I'm not the only one with such questions, so I did my research and wrote this article on burner phones and in which instances they can be helpful to bot...
Author: Janet Kathalu |
|
|
|
|
30
|
How to Unlock Computer Screen Windows 10? |

|
Upon leaving your computer unattended, the windows screen automatically turns off after a while, and you would need to unlock it for further access and resume working. There are several methods to unlock Windows 10 regardless you know the passw...
Author: Tithi Raha |
|
|
|
|
31
|
How to Check If an Email Is Legit? |

|
“Phishing” is a popular term among hackers and hacking sites. These phishing emails are sent with the primary purpose of stealing valuable information or taking control of your networks.
It’s reported that every day nearly 3.4 billion phishing emai...
Author: Tithi Raha |
|
|
|
|
32
|
Can My Employer Monitor My Work Computer At Home? |

|
An employer has every right to monitor the work computers of their employees at home. The employer will do so for various reasons: they will need to ensure their employees' productivity. It is also for the protection of the organization's software ...
Author: Gloria Mutuku |
|
|
|
|
33
|
What Are Ethical and Unethical Practices Related to Internet Use? |
|
Information technology has made the world more accessible than ever in history. Different people from different parts of the world have the ability to access the internet and simultaneously make use of online resources. Do not be deceived that what...
Author: Ian Musyoka |
|
|
|
|
34
|
How Does Cloud Sharing Work |
|
Whether you are a business dealing with loads of information or an individual saving personal files, data is an integral part of day-to-day activities. Handling data is a standard process, and as you collect, save, and share information, it is essent...
Author: Eunice Njuguna |
|
|
|
|
35
|
What Does a Firewall Do? |
|
Before I started writing this, I thought to myself, “Who really needs a firewall?” But, as it turns out, most of us do. If your personal or company computer is connected to the internet, your network is always exposed to threats and risks. This mea...
Author: Ian Musyoka |
|
|
|