|
1
|
What Does a Computer Repair Topeka KS Technicians Do |

|
Computer Repair Topeka, KS technicians perform all the necessary steps to repair the malfunctioning computer software and hardware. Upon calling a technician, they will first diagnose the issues with your computer system and ensure all are returned t...
Author: Tithi Raha |
|
|
|
|
2
|
Can Humans Read Binary Code Unlock the Secrets of Binary |

|
Have you ever wondered if humans can read binary code? If you're like many others, you may have encountered binary code in your computer science studies or even in your daily use of technology, but never quite understood how to read it. Well, you're ...
Author: Newton Waweru |
|
|
|
|
3
|
Understanding SSID: What Is It and How Does It Work? |

|
Understanding SSID: What Is It and How Does It Work?
Wireless networks have become increasingly popular, enabling people to connect to the Internet and access network resources without the need for wired connections. One of the key components of wir...
Author: James Fleming |
|
|
|
|
4
|
Is Binary Worth Learning? Know the Benefits of Learning Binary Code |

|
Are you wondering if learning binary is worth your time and effort? Discover the benefits of binary and see how it can enhance your career opportunities.
As a whole, learning binary can bring a multitude of benefits for individuals looking to en...
Author: Newton Waweru |
|
|
|
|
5
|
Binary Code vs. Morse Code: A Head to Head Analysis |

|
Seeking to comprehend the difference between Binary Code and Morse Code? Your search ends here. In this write-up, I will delve into a side by side examination of these two codes and examine their specific features and uses.
As a whole, Binary Code a...
Author: Newton Waweru |
|
|
|
|
6
|
Binary code VS ASCII [Understanding the Differences] |

|
This piece delves into the differences between binary and ASCII coding methodologies. If you're seeking information and a thorough examination of these coding techniques, your search has come to an end. I understand the confusion that comes with comp...
Author: Newton Waweru |
|
|
|
|
7
|
How to Fix My Microphone Doesn’t Work on Windows 11 |

|
How to Fix My Microphone Doesn't Work on Windows 11
Have you ever been on a vital video call and encountered your microphone unexpectedly ceasing to work? It can be incredibly frustrating. Unfortunately, it's an all too common issue with Windows 11;...
Author: James Fleming |
|
|
|
|
8
|
Will Downloading Slow Down My Internet? How to Fix it? |

|
Your internet speed may slow down when one user on your Wi-Fi connection is downloading large-sized files or downloading multiple files at the same time. The same thing will happen when you upload large files as well. So, you may notice a connection ...
Author: Tithi Raha |
|
|
|
|
9
|
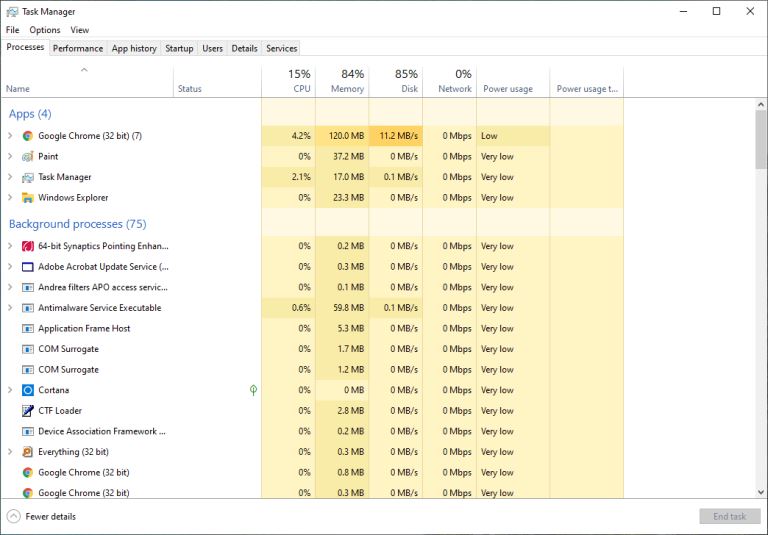
Why Do Games Download Slow On PC? Check Out The Solution! |

|
Sometimes you will notice that your computer is downloading files at an extremely poor speed. Whether it could be your ISP or faulty hardware of your PC, connection interruption can be quite frustrating. If you've to wait for the entire day just to d...
Author: Tithi Raha |
|
|
|
|
10
|
10 Undeniable Benefits of Remote Assistance |

|
Advancements in technology have led to several changes in how we live and work. One of the most significant changes has been the rise of remote working. With the ability to connect to the internet from anywhere in the world, more and more people are ...
Author: Faith Cheruiyot |
|
|
|
|
11
|
How Real Network Setup Problems Are Solved |

|
Network setups are not always smooth as per the expectations many users have. You encounter several issues which one must know how to fix them. It affects the team, reducing its efficiency and productivity. One must learn how to handle those issues w...
Author: Faith Cheruiyot |
|
|
|
|
12
|
Network Setup Tutorial - Configuring a Remote Access Server |

|
Many offices have many users and teams with multiple branches. Using remote access servers enables businesses and organizations to let their staff access all the devices remotely. It mainly works in areas where the users cannot access the local area ...
Author: Faith Cheruiyot |
|
|
|
|
13
|
How Do You Locate Someone's IP Address? 4 Ways to Apply! |

|
An IP address is a simple numeric address used for identifying unique devices in a network. You can easily find the IP address of your own, but there are times when you may need to locate someone's IP address. Maybe you want to blacklist them or you ...
Author: Tithi Raha |
|
|
|
|
14
|
Monitor Repair: How Can I Discard Monitor Screen Safely |

|
Have you ever wondered how to dispose of an old computer monitor screen properly? If so, you're not alone. With the growing amount of electronic waste, it's important to know how to safely recycle or discard items like screens.
There are several way...
Author: Faith Cheruiyot |
|
|
|
|
15
|
Tablet Repair: Common Tablet Problems And Solutions |

|
After spending so much money on your new tablet, the expectations are always high. Many users dont have expectations of getting problems, thats not the reality. Tablet users experience several problems, and there are ways one can fix them.
The are ...
Author: Faith Cheruiyot |
|
|
|
|
16
|
How to Fix a Stereo Receiver That is Not Making Sound |

|
Are you having an issue with your stereo sound receiver? Is the power on, but you are receiving no sound from your speakers? In such a case, a troubleshooting procedure can help fix the problem before tossing off your remote or disconnecting any wire...
Author: Faith Cheruiyot |
|
|
|
|
17
|
How to Secure Your New Computer Against Viruses and Malware |

|
Do you have a new computer at home, at your workplace, or in your business? Are you worried that viruses and malware may attack your setup? You can use several ways to ensure that your new setup is safe from viruses and malware.
There are many cases...
Author: Caroline Chebet |
|
|
|
|
18
|
How Does a Computer Work: A Definitive Guide |

|
A computer is an electronic machine that acts as an information processor. It takes the raw information or data, stores it, works on it, and spits the result out. However, there is an entire process behind how the computer works.
A computer is desi...
Author: Tithi Raha |
|
|
|
|
19
|
Can You Get a Keylogger Just by Visiting a Website? |

|
Ever since malware and virus infections have started to increase at a rapid pace, the fear of getting a keylogger just by visiting a website is bothering many people. After all, a majority of internet users access a lot of websites on a daily basis. ...
Author: Tithi Raha |
|
|
|
|
20
|
What is the Internet of Things IoT |

|
The Internet of things (IoT) is a general term for the increasing number of electronics that are not conventional computer equipment but connected to the Internet to send information, receive instructions, or both.
Tech analyst company IDC forecasts...
Author: Collins Okoth |
|
|
|
|
21
|
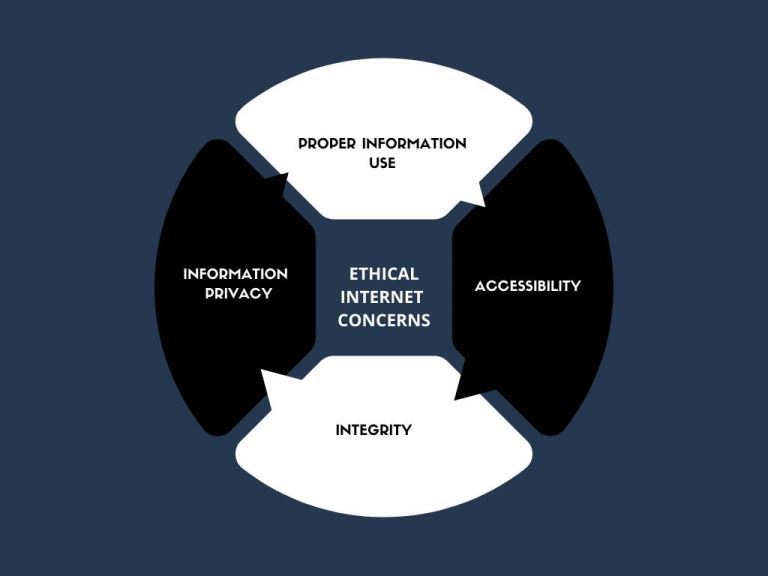
What Are Ethical and Unethical Practices Related to Internet Use? |
|
Information technology has made the world more accessible than ever in history. Different people from different parts of the world have the ability to access the internet and simultaneously make use of online resources. Do not be deceived that what...
Author: Ian Musyoka |
|
|
|
|
22
|
Why Do We Need Ethics for Internet Users? |

|
With the introduction of computers globally in the 1990s, the entire approach of working, communicating, and storing important information has changed. I mean, who would have thought that a machine can make one convey a message at any corner of the w...
Author: Collins Okoth |
|
|
|
|
23
|
Best Solutions to Computer Overheating |

|
Overheating in computers is often experienced by users when playing games. Even though it can be disturbing, the situation can be fixed. Overheating of the computer when playing games can be greatly attributed to insufficient cooling. It can make the...
Author: James Fleming |
|
|
|
|
24
|
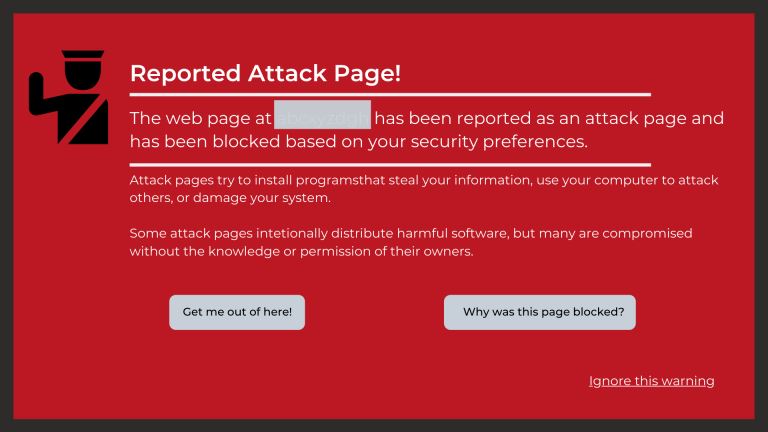
What Are the Signs a Website Has Been Hacked? |
|
If you own a business, you likely depend a lot on your website. From eCommerce to marketing, your website is the backbone of your transactions and everything in between. Without its help, you could face a lot of setbacks. Nevertheless, many business...
Author: Ian Musyoka |
|
|
|
|
25
|
My Computer is Running Slow, What Steps Can I Take to Fix It? |
|
Using a slow computer can make the simplest of jobs feel very irritating and cumbersome. Your files take forever to launch, your browser keeps hanging, words you type do not show up on time, and you keep getting the ‘Not Responding’ error message whe...
Author: Ian Musyoka |
|
|
|
|
26
|
How Do I Set Up a New User on My Computer Windows 10 |

|
When installing Windows 10, the first account you create is an Administrator’s account. An administrator’s account has several privileges, and a common one is the ability to add new users to your computer.
There are several reasons an administrator...
Author: Eunice Njuguna |
|
|
|
|
27
|
What Happens When a Site I Use Gets Hacked? |

|
In the Internet’s virtual world, security is very confusing as compared to the real world. Security is messy; difficult to develop and sustain. As much as the Internet is built around a system of protocols, these rules can often be ignored.
When...
Author: Ian Musyoka |
|
|
|
|
28
|
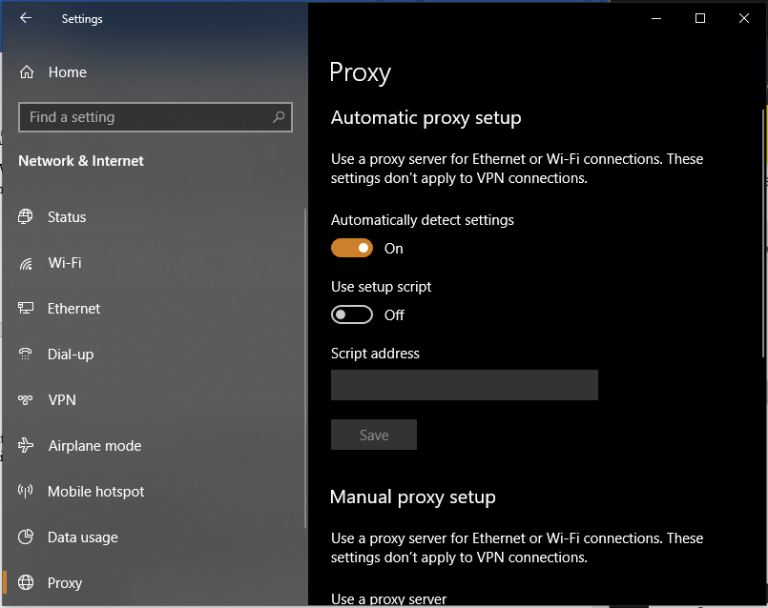
What are Proxy Server Ports? |
|
Proxy servers are dedicated software systems that run on a computer and are intermediaries between two endpoint devices. These endpoint devices are usually a personal computer and a server. A server is a central computer from which other computers (c...
Author: Collins Okoth |
|
|
|
|
29
|
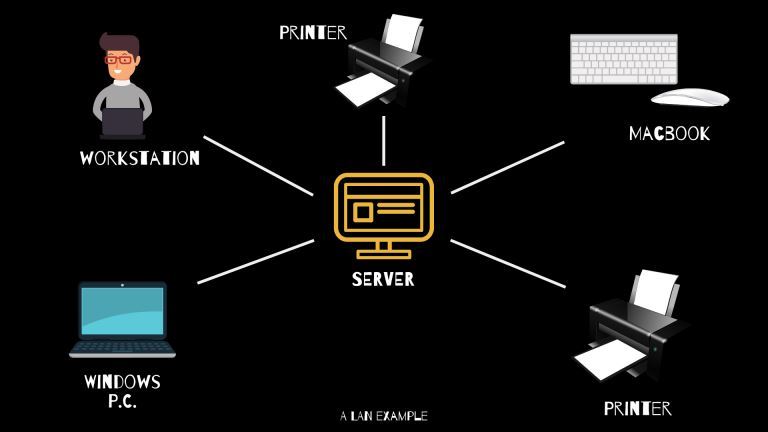
What Is WAN/LAN? |
|
Every day, computer networks grow in size and popularity. As the internet keeps stretching to other parts of the globe, the exchange of information among computers is constantly increasing. Understanding the connections that allow computer networks t...
Author: Ian Musyoka |
|
|
|
|
30
|
What Do I Need to Upgrade for Better Gaming? |

|
The majority of windows-based PCs found in stores such as Walmart and Best Buy do not have the capabilities to run newer video games. These "White label" computers sport boring designs and poor processing speeds making them unsuitable for the gaming ...
Author: Delilah Daut |
|
|
|
|
31
|
How to Remove Malicious Software |

|
Malware is software designed to damage, gain access to, or disrupt the normal functioning of the computer. Malware is valuable to cybercriminals because they use it to extract sensitive information, prevent access to the device, and steal money. The ...
Author: Delilah Daut |
|
|
|
|
32
|
How Do I Find My IP Address |
|
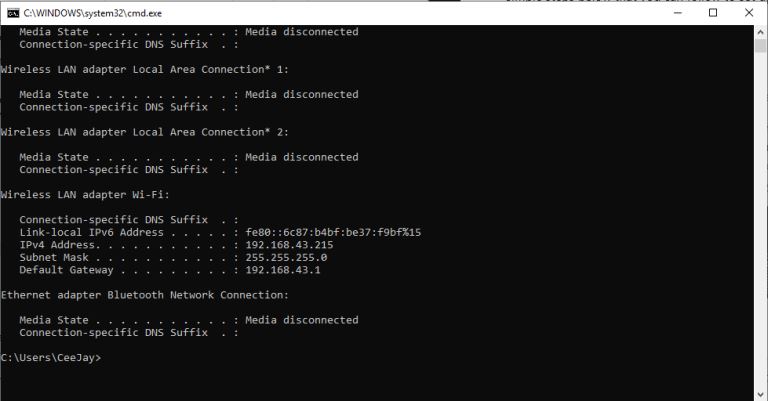
The internet is a worldwide network of unrelated computers yet able to communicate successfully by following a specific set of rules. These rules are commonly known as protocols. A fundamental yet essential tenet of the internet is the Internet Proto...
Author: Collins Okoth |
|
|
|
|
33
|
What Is a VPN? |
|
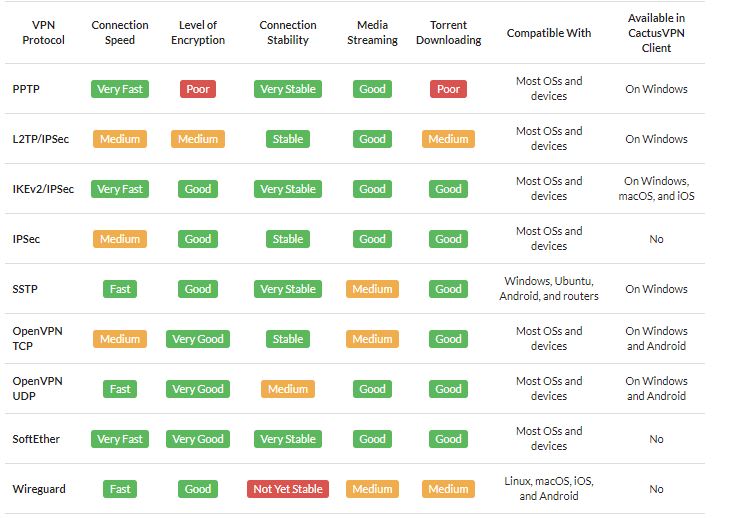
A VPN is short for Virtual Private Network. It is a collection of several networking schemes that allow computers to utilize public internet lines by creating a virtual network. VPNs have no specific standard models; however, it typically uses the pu...
Author: Collins Okoth |
|
|
|
|
34
|
What Is Processor Virtualization Technology? |

|
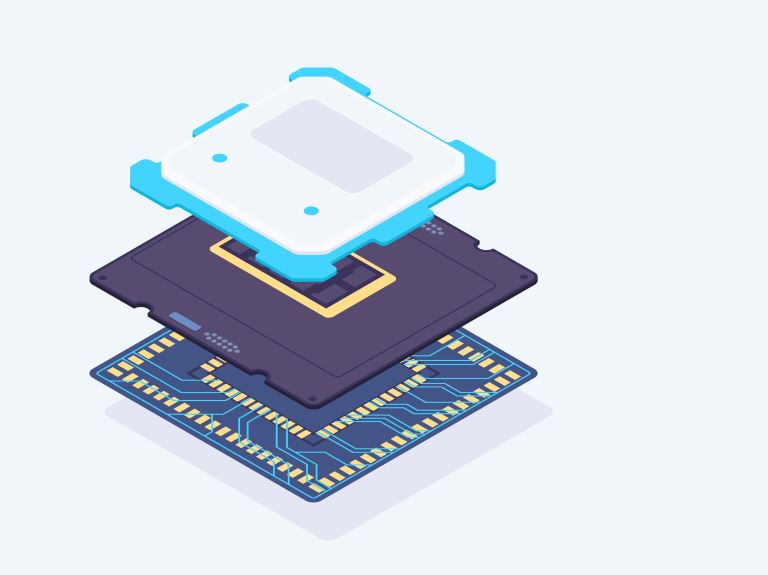
In computing, many things can be made virtual, and there are various types of virtualization: network, desktop, and application virtualization. There are some challenges involved in the virtualization of modern processors (i.e., those built on x86 ar...
Author: Trey Williams |
|
|
|
|
35
|
What Is a Computer Processor Thread |
|
The brief answer to this question is that, in computer processing, a thread is a short sequence of programmed instructions or code.
But that’s not very helpful all by itself.
So, to properly understand what a computer processor thread is and what ...
Author: Trey Williams |
|
|
|