|
1
|
When Is Binary Code Used? Understanding its Uses in Technology |

|
Are you curious about when binary code is used? Look no further. This article will explore the common uses of binary code in technology and how it plays a role in the functioning of computers and digital devices.
As a whole, binary code is used in a...
Author: Newton Waweru |
|
|
|
|
2
|
Searching for a Song by Humming on Google |

|
Finding a song through humming can be challenging, but with the help of Google and other tools, it is possible to identify the song you have in mind.
Here Are Some Steps You Can Follow to Find a Song on Google Through Humming:
Start by humming th...
Author: James Fleming |
|
|
|
|
3
|
Where to Find Information on In-home Computer Service Online |

|
If you're like most people, your computer is an important part of your life. You use it for work, school, entertainment, and communication. When something goes wrong with it, it can be a huge inconvenience. Many people use in-home computer services i...
Author: Faith Cheruiyot |
|
|
|
|
4
|
Quick Steps on how to set Google Chrome as a Default Browser |

|
The whole process of setting Chrome as your PC's default browser varies depending on the PC operating system. So it is right for us to say that different operating systems have different ways in which you can customize your computer to achieve Chrome...
Author: James Fleming |
|
|
|
|
5
|
The 10 Best Web Browsers for Windows in 2022 |

|
Today's web is a constantly moving target, and the web browsers we use to navigate it have changed. Browsers come and go pretty regularly, and each new release typically brings a host of new and exciting features that set it apart from its predecesso...
Author: James Fleming |
|
|
|
|
6
|
Beginner Guide: How to Become an Ethical Hacker |

|
Dreaming to become an ethical hacker is one thing and becoming one in another one. It is not an easy ride in the park. The challenges and rough rides are part of the ethical hacker's journey. Allow me to take you the best ways to become an ethical ha...
Author: Berts Njoroge |
|
|
|
|
7
|
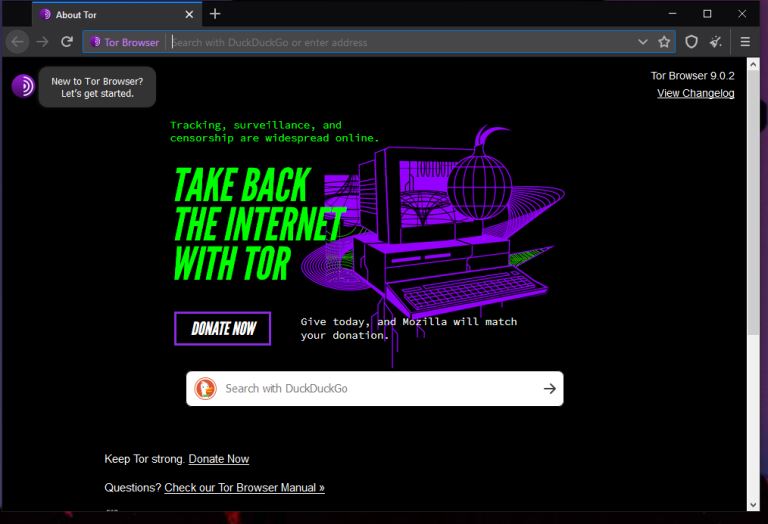
What things can you do on the dark web? |

|
Have you always wondered what goes on in the dark web? I understand your curiosity, and I am here to break down all you need to know about the dark. Anything in darkness will be brought to light, literally.
There are a lot of activities that happen...
Author: Berts Njoroge |
|
|
|
|
8
|
What is HTTPs, and Why Should I Care about it? |

|
Most people often confuse HTTP and HTTPs, some think they can be used interchangeably, and so on. However, there is a simple and clear difference between HTTP and HTTPs in computer networking. Simply put, HTTPs is an abbreviation for Secure Hypertex...
Author: Collins Okoth |
|
|
|
|
9
|
How Do Search Engines Work? |

|
You’re in the kitchen making your mom’s favorite pizza. To get topping ideas, you open your web browser to perform a search. You type ‘topping ideas’ in the search box, hit ‘Enter,’ and get eighty-nine million results in about half a second. For th...
Author: Ian Musyoka |
|
|
|
|
10
|
What Happens When a Site I Use Gets Hacked? |

|
In the Internet’s virtual world, security is very confusing as compared to the real world. Security is messy; difficult to develop and sustain. As much as the Internet is built around a system of protocols, these rules can often be ignored.
When...
Author: Ian Musyoka |
|
|
|
|
11
|
What is The Darknet? |
|
The US Department of Defense developed an encrypted and anonymized network in the late ‘90s. The intention behind developing this network was to operate a secure and inaccessible network that would offer absolute protection and shielding from US Gove...
Author: Collins Okoth |
|
|
|
|
12
|
How To Clear Your Cache |

|
If you've ever struggled to access specific websites or failed to load an image on a webpage, no matter how many times you hit refresh, you've probably been advised to “clear your cache.” In fact, the only phrase more common in the world of IT and te...
Author: Trey Williams |
|
|
|