|
1
|
What are the Challenges Faced in Cybersecurity Risks and Solutions |

|
Cybersecurity is a growing concern, and navigating its challenges can be daunting. You're not alone in seeking help; I'm here to provide the guidance you need. This article dives into the key obstacles faced in cybersecurity, offering practical insig...
Author: Newton Waweru |
|
|
|
|
2
|
Methods You Can Use to Protect Yourself from Social Engineering |

|
With the digital world evolving, the risk of social engineering has become a concern for many. Leveraging our expertise, we can arm you with methods to protect yourself against social engineering threats. This article will detail effective strategies...
Author: Newton Waweru |
|
|
|
|
3
|
What is a Possible Effect of Malicious Code |

|
Navigating the digital world can feel like a labyrinth, especially when malicious code lurks in the shadows. It's alarming, I know. But fear not; I've delved into this complex issue to help guide you. In this article, we'll illuminate the potential e...
Author: Newton Waweru |
|
|
|
|
4
|
Types of Cybersecurity Threats Identifying Key Risks |

|
Cybersecurity threats are a growing concern in our digital age, and staying informed is essential. As someone who understands your need for help, I've delved into this topic to provide you with valuable insights. This article will cover various cyber...
Author: Newton Waweru |
|
|
|
|
5
|
The Biggest Cybersecurity Attacks Recorded |

|
Curious about the world of cybersecurity? To keep you informed, I have delved into the most massive cyber attacks ever recorded. Let's explore the critical incidents, their impact, and ways to stay protected together. By the end of this article, you'...
Author: Newton Waweru |
|
|
|
|
6
|
How Does Biometrics Change the Face of Security Enhancing Security |

|
Navigating the world of security can seem like a daunting task. With new technologies like biometrics rising, feeling curious and overwhelmed is normal. This article will guide you through how does biometrics change the face of security, providing in...
Author: Newton Waweru |
|
|
|
|
7
|
Cyber Espionage and Information Warfare Threats to National Security |

|
Cyber Espionage & Information Warfare can be daunting, but don't worry - we're here to help. As someone who's delved into this complex topic, I empathize with your need for guidance. This article offers clear, human insights into the critical aspects...
Author: Newton Waweru |
|
|
|
|
8
|
Methods that Employees Can Expose Company Data Accidentally |

|
Concerned about employees accidentally exposing company data? You're not alone. I've delved into this issue, and I'm here to help. In this article, I'll explore standard methods that can lead to unintentional data leaks so that you can take preventiv...
Author: Newton Waweru |
|
|
|
|
9
|
The History of Cybersecurity and Hacking A Detailed Guide |

|
I understand your interest in the history of cybersecurity and hacking, as it's a fascinating subject. Rest assured, I've delved deeply into the topic and will guide you. This article will explore key milestones and developments that shaped this ever...
Author: Newton Waweru |
|
|
|
|
10
|
The Danger of Mixing Cyberwarfare with Cyber Espionage |

|
Are you concerned about the potential hazards of combining cyber warfare and cyber espionage? You're not alone. As someone who has delved deep into this critical issue, I understand your concerns and am here to help. This article will explore the ris...
Author: Newton Waweru |
|
|
|
|
11
|
How Can an Intrusion Detection System Protect Your Company |

|
Concerned about your company's cybersecurity? An Intrusion Detection System (IDS) might be your perfect solution. I understand how critical it is to protect sensitive data, and I've delved into the topic to provide the guidance you need.
An intrusi...
Author: Newton Waweru |
|
|
|
|
12
|
How to Protect Yourself from Cyberstalking Stay Safe Online |

|
Are you concerned about cyberstalking and your online safety? You're not alone. As an individual who delved into this issue, I empathize with your worries. In this article, I'll discuss practical steps to protect yourself from cyberstalking, so you c...
Author: Newton Waweru |
|
|
|
|
13
|
How to Protect Your Company Against Cyber Espionage |

|
Concerned about cyber espionage threatening your business? You're not alone. As an experienced researcher, I understand the need to stay vigilant. In this article, I'll explore practical steps to safeguard your company, providing you with the tools t...
Author: Newton Waweru |
|
|
|
|
14
|
Where Will Cyber Security be 10 Years from Now Navigating the Future |

|
As we navigate an increasingly digital world, you might wonder where cyber security will be in 10 years. After researching extensively, I'm confident in sharing valuable insights. This article will explore future cyber security trends and challenges...
Author: Newton Waweru |
|
|
|
|
15
|
Cybersecurity Expectations vs Reality What You Need to Know |

|
Are you eager to learn about cybersecurity but feel overwhelmed by the jargon and technicalities? You're not alone, as many people find themselves navigating this intricate landscape with high expectations, only to be met with realities that often fe...
Author: Newton Waweru |
|
|
|
|
16
|
The Next Big Thing in Cyber Security Discover Innovative Solutions |

|
Ready to uncover the Next Big Thing in Cyber Security? You're not alone! As cyber threats evolve, so should our defenses. Fear not, I've delved deep into this crucial issue to help you stay informed and prepared. Join me in this article as we explore...
Author: Newton Waweru |
|
|
|
|
17
|
What Are the Five Pillars of Cloud Security |

|
Addressing the security challenges in cloud computing requires an understanding of the pillars. A company needs insight into shared responsibility in managing data, privileges, users, and resources. Cloud security requires frameworks to ensure all po...
Author: Eunice Njuguna |
|
|
|
|
18
|
How to Set a Different Wallpaper On Each Monitor In Windows 10 and 11 |

|
How to Set a Different Wallpaper On Each Monitor In Windows 10 and 11
Introduction
Setting a chosen wallpaper is an essential personalization function that most new PC owners utilize. However, viewing the same wallpaper can become tedious if you ha...
Author: Melanie Fleming |
|
|
|
|
19
|
Can Binary Code Be Used for Hacking? Uncover the Truth |

|
Are you eager to learn about the possibilities of using binary code for hacking? My comprehensive article explores the reality of binary code's capabilities in the realm of hacking.
In general, binary code can be applied as a technique in the field ...
Author: Newton Waweru |
|
|
|
|
20
|
How to Develop a Cloud Strategy | A step-by-step Guide |

|
When developing a cloud strategy, it's important to outline the best services and tools for a cloud solution. Your cloud strategy should include leveraging the company's IT capabilities with business needs that yield the most benefit from cloud compu...
Author: Eunice Njuguna |
|
|
|
|
21
|
How Can I Tell If Cloud Computing Is Right For My Company? |

|
Cloud computing is right for you if your company needs support with data storage, infrastructure scaling, big data analytics, networking, backup service strategies, and application development. A business looking to boost productivity, create room fo...
Author: Eunice Njuguna |
|
|
|
|
22
|
Is Binary Code Hard To Learn? Become a Binary Code Expert |

|
It's okay; figuring out binary code doesn't have to be challenging! I've done some research on the subject and am here to assist. I comprehend the requirement to acquire new abilities and can direct you through the journey. In this piece, we'll delve...
Author: Newton Waweru |
|
|
|
|
23
|
NFC Guide: All You Need to Know About Near Field Communication |

|
As technology advances and smartphones become practically ubiquitous, the need for Near Field Communication (NFC) is rapidly increasing. NFC allows two electronic devices to wirelessly communicate with each other when touching or just by being in c...
Author: James Fleming |
|
|
|
|
24
|
What Are Your Strategies To Avoid Being A Victim Of Cybercrime? |

|
Cybercrimes have been on the increase, with many unaware victims. When we hear about cybercrimes, we automatically think about hackers. But cybercrime is not just about hacking. It goes beyond that. Many people today use their devices, such as phones...
Author: James Fleming |
|
|
|
|
25
|
How to Configure Email Client To Send Mail Through My Own SMTP Server? |

|
SMTP is the internet standard for sending and receiving emails. Email clients use SMTP to send messages to a mail server, while email servers use it to forward messages to their recipients. You need to enter your SMTP settings to use the email from a...
Author: Faith Cheruiyot |
|
|
|
|
26
|
What are the Different Types of Tutorials? |

|
Do you always think about where you can learn how to do something? Most people look for tutorials to help them how to do tasks. Watching these videos gives you a deeper understanding and techniques for doing things better. It could be, installing ele...
Author: Faith Cheruiyot |
|
|
|
|
27
|
What iPad Repair Strategies You Should Try Today |

|
iPads are unique devices that have revolutionized the way we work and play. But like all electronic gadgets, they can sometimes malfunction or break. If your iPad needs repair, don't worry - you're not alone! Thousands of people each year find themse...
Author: Faith Cheruiyot |
|
|
|
|
28
|
What are the Data Recovery Tips & Tricks? |

|
There is a lot of evolution around data recovery, with many individuals starting data recovery businesses. We have many tricks and tips that make the whole process efficient. Data loss happens in different situations, and it can be very frustrating. ...
Author: Faith Cheruiyot |
|
|
|
|
29
|
What Are The Best Backup Services Strategies You Should Try? |

|
Are you aspiring to perform data recovery in your organization or want to hire someone? Before starting over, it is a wise idea that you understand the best backup services strategies.
There are several important backup services strategies users in ...
Author: Faith Cheruiyot |
|
|
|
|
30
|
How Do I Structure a Tutorial? Easy Steps |

|
How can you structure a tutorial to ensure your audience gets the best lesson? What structure should your tutorial content have? Tutorial structures are essential in imparting knowledge and teaching skills. You should understand what format to use in...
Author: Faith Cheruiyot |
|
|
|
|
31
|
What are the backup best practices using the cloud? |

|
Have you ever imagined what you would do if you lost all your crucial data? Of course, you cant imagine. Well, there is only one way to be sure of data safety and longevity- data backup. And the best thing is; cloud backup is here to make it easy to ...
Author: Faith Cheruiyot |
|
|
|
|
32
|
Why Do We Need Ethics for Internet Users? |

|
With the introduction of computers globally in the 1990s, the entire approach of working, communicating, and storing important information has changed. I mean, who would have thought that a machine can make one convey a message at any corner of the w...
Author: Collins Okoth |
|
|
|
|
33
|
A Detailed Guide to Removing Ransomware in Windows 10 |
|
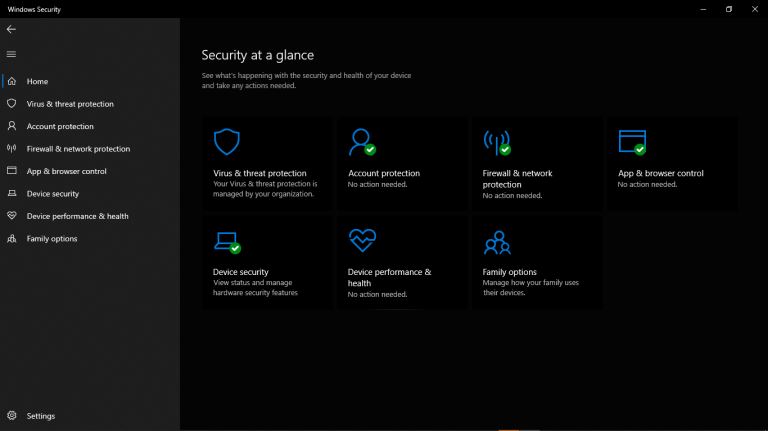
One of the main problems faced by internet companies today is Ransomware. For this reason, cybersecurity has continued to grow as an industry in general. Unfortunately, players on both sides can easily be described as the bad guys and the good guys. ...
Author: Collins Okoth |
|
|
|
|
34
|
What is Ransomware How it Works and How to Remove it |

|
Ransomware has grabbed the attention of many internet users, governments, and internet companies in recent years. Although Ransomware has been in existence for a long time, its effects have continued to be felt. Ransomware is short for Ransom Malware...
Author: Collins Okoth |
|
|
|
|
35
|
How Do I Stop Emails Going to Spam Folder |
|
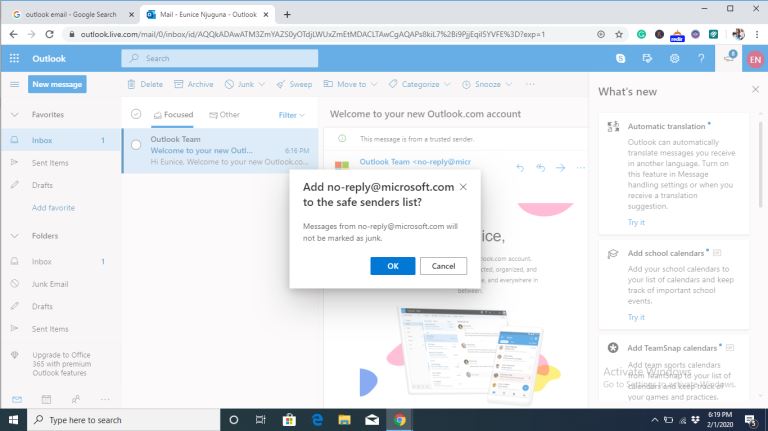
Gmail, Yahoo, Hotmail, AOL, and Outlook are all excellent email services. They offer efficient email services by ensuring the proper delivery of emails to the inbox folder. But even with the efficiency in their services, there are negative issues tha...
Author: Eunice Njuguna |
|
|
|