|
1
|
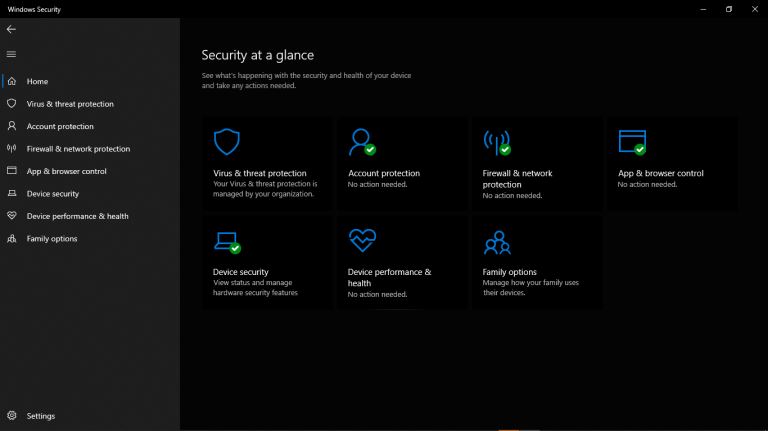
My Account Has Been Hacked What Do I Do Secure Your Information |

|
Facing a hacked account can be a nightmare, and I understand your anxiety. Rest assured, I've delved deep into this issue and am here to help! This article will empathetically walk you through the essential steps to regain control and secure your acc...
Author: Newton Waweru |
|
|
|
|
2
|
What Are the Five Pillars of Cloud Security |

|
Addressing the security challenges in cloud computing requires an understanding of the pillars. A company needs insight into shared responsibility in managing data, privileges, users, and resources. Cloud security requires frameworks to ensure all po...
Author: Eunice Njuguna |
|
|
|
|
3
|
What Are The Duties of a Computer Repair Technician in Topeka KS |

|
From diagnosing initial issues to finding a solution, a computer repair technician in Topeka or any other area is responsible for all phases of the entire repair process. Moreover, the primary duty of a repair technician is to leave your device funct...
Author: Tithi Raha |
|
|
|
|
4
|
Is it Cheaper to Repair or Replace a Computer |

|
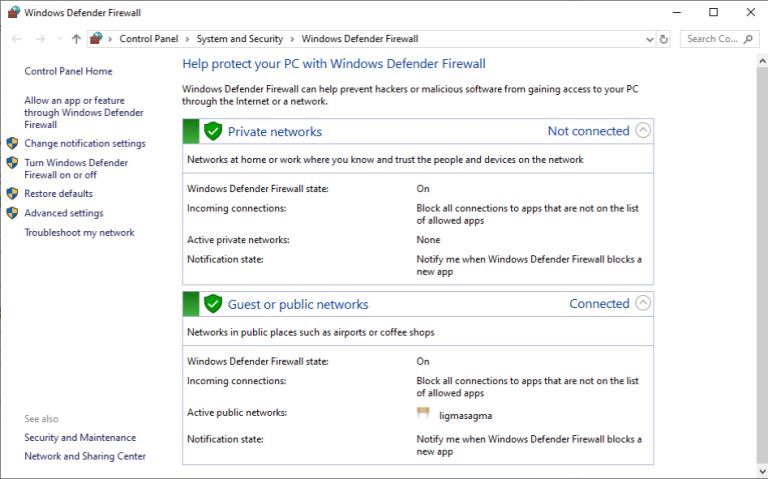
It's certain that no computer will last forever. But, to yield the best benefits out of your investment, you would want to stretch the life out as long as possible. And, computer repairs can really help you stretch out the life of your devices. Yet, ...
Author: Tithi Raha |
|
|
|
|
5
|
Is Binary Worth Learning? Know the Benefits of Learning Binary Code |

|
Are you wondering if learning binary is worth your time and effort? Discover the benefits of binary and see how it can enhance your career opportunities.
As a whole, learning binary can bring a multitude of benefits for individuals looking to en...
Author: Newton Waweru |
|
|
|
|
6
|
How to Set a Different Wallpaper On Each Monitor In Windows 10 and 11 |

|
How to Set a Different Wallpaper On Each Monitor In Windows 10 and 11
Introduction
Setting a chosen wallpaper is an essential personalization function that most new PC owners utilize. However, viewing the same wallpaper can become tedious if you ha...
Author: Melanie Fleming |
|
|
|
|
7
|
Binary Code vs. Source Code [Know the Difference] |

|
In this article, we'll delve into the differences between binary code and source code and provide examples to assist in understanding the usage and application of each in the realm of computer programming. Whether you're a beginner or an experienced ...
Author: Newton Waweru |
|
|
|
|
8
|
Can Binary Code Be Used for Hacking? Uncover the Truth |

|
Are you eager to learn about the possibilities of using binary code for hacking? My comprehensive article explores the reality of binary code's capabilities in the realm of hacking.
In general, binary code can be applied as a technique in the field ...
Author: Newton Waweru |
|
|
|
|
9
|
What Security Parameters are Present in the Cloud? |

|
The security parameters present in the cloud are the technologies designed to counter internal and external threats. They include data loss prevention applications, disaster recovery tools, and identity access management systems. Most cloud security ...
Author: Eunice Njuguna |
|
|
|
|
10
|
How to Develop a Cloud Strategy | A step-by-step Guide |

|
When developing a cloud strategy, it's important to outline the best services and tools for a cloud solution. Your cloud strategy should include leveraging the company's IT capabilities with business needs that yield the most benefit from cloud compu...
Author: Eunice Njuguna |
|
|
|
|
11
|
Complete Guide on How to Upgrade to Windows 10 From Windows 7 for Free |

|
Complete Guide on How to Upgrade to Windows 10 From Windows 7 for Free
Are you using Windows 7 and wondering how to upgrade to Windows 10 for free? Worry no more! Microsoft released a special upgrade offer for users of Windows 7 who want to upgrade ...
Author: James Fleming |
|
|
|
|
12
|
Deciphering the World of Computer Acronyms: A Must-Know List |
|
Deciphering the World of Computer Acronyms: A Must-Know List
As technology continues to advance and evolve, it can be overwhelming to keep up with all the diff erent acronyms thrown around in the world of computers. There are so many other terms and...
Author: James Fleming |
|
|
|
|
13
|
What Are Your Strategies To Avoid Being A Victim Of Cybercrime? |

|
Cybercrimes have been on the increase, with many unaware victims. When we hear about cybercrimes, we automatically think about hackers. But cybercrime is not just about hacking. It goes beyond that. Many people today use their devices, such as phones...
Author: James Fleming |
|
|
|
|
14
|
How To Protect the phone From Hackers Using Smart Security at Home app |

|
Every day, there's a new headline about a major company being hacked. While it's important to keep up with the latest security news, it's also essential to know how to protect your devices from hackers and scammers.
There are many ways hackers can g...
Author: Faith Cheruiyot |
|
|
|
|
15
|
Tips on Securing Your Computer From Hackers |

|
Are you concerned about the security of your computer? You should be, Hackers are becoming increasingly sophisticated, and they can easily steal your data or infect your computer with a virus if you're not careful.
There are different ways of secur...
Author: Faith Cheruiyot |
|
|
|
|
16
|
What Are The Modern Rules of In-home Computer Service? |

|
In the olden days, if your computer crashed or stopped working, you had to take it in for servicing. But now, with so many people working remotely and relying on their computers, there are new rules for when and how you should get your computer servi...
Author: Faith Cheruiyot |
|
|
|
|
17
|
How To Protect Yourself in an Internet Security Breach |

|
Since the advent of the Internet, online security has been a concern for both individuals and businesses. Unfortunately, despite our best efforts, cyberattacks continue to occur with alarming frequency.
There are several things you can do to safegu...
Author: Faith Cheruiyot |
|
|
|
|
18
|
How Do You Find Your Router's IP Address? |

|
Without knowing your router's IP address, you can't make any changes to it. Whether you want to create a new password for your Wi-Fi, change the name of your network, or switch to a different channel for boosting your connection, an IP address is a m...
Author: Tithi Raha |
|
|
|
|
19
|
New Computer Setup: What are the must-have programs on your new PC? |

|
Did you purchase a new PC? Congratulations! To get the most out of it, you need to add must-have programs to your new computer.
There are many must-have apps you need to install during your new computer setup. For Example, typing programs like notep...
Author: Caroline Chebet |
|
|
|
|
20
|
Bluetooth hacks: How to hack a car's Bluetooth? |

|
Bluetooth hacking is one of the most familiar hacks that hackers use. If you are a car owner, you must take precautions to keep your car safe from hackers. I want to keep myself and my car safe; that's why I researched and wrote this article to guide...
Author: Janet Kathalu |
|
|
|
|
21
|
My C Drive Is Full Without Reason, Ways to Solve It |

|
Computers store the system files within the drive C, and there are some instances when your device may give you a warning that this part of your hard drive is filled up. While it can fill up from file storage, in other cases, it could be due to other...
Author: Gloria Mutuku |
|
|
|
|
22
|
What Does a Virus Scan Actually Do: A Definitive Guide |

|
A virus scan runs through a computer system to check malicious threats and remove them. There are two types of protection provided by antivirus software during a virus scan. This includes proactive and reactive protection. The former spots potential ...
Author: Tithi Raha |
|
|
|
|
23
|
Beginner Guide: How to Become an Ethical Hacker |

|
Dreaming to become an ethical hacker is one thing and becoming one in another one. It is not an easy ride in the park. The challenges and rough rides are part of the ethical hacker's journey. Allow me to take you the best ways to become an ethical ha...
Author: Berts Njoroge |
|
|
|
|
24
|
Password Security: How to Create a Strong Password (and Remember It) |

|
Have you ever typed a password and the system indicates that it is too weak or you add some symbols or numbers? As common as it is, a strong password saves you from intrusions and cyber attacks. It's hard to create a strong and memorable password wit...
Author: Fay Kokri |
|
|
|
|
25
|
What things can you do on the dark web? |

|
Have you always wondered what goes on in the dark web? I understand your curiosity, and I am here to break down all you need to know about the dark. Anything in darkness will be brought to light, literally.
There are a lot of activities that happen...
Author: Berts Njoroge |
|
|
|
|
26
|
What is HTTPs, and Why Should I Care about it? |

|
Most people often confuse HTTP and HTTPs, some think they can be used interchangeably, and so on. However, there is a simple and clear difference between HTTP and HTTPs in computer networking. Simply put, HTTPs is an abbreviation for Secure Hypertex...
Author: Collins Okoth |
|
|
|
|
27
|
Windows 10: How to login to Windows 10 without password? |

|
You won’t want to go through a password recovery process if you lose your password, which can be tiresome and hectic.
We will look at the best four poss
Use Microsoft website to set login preferences
Use advanced password managers- recommended...
Author: Fay Kokri |
|
|
|
|
28
|
Computer Repair: How to Detect Crypto Mining Malware |

|
The vast growth of the cryptocurrency market has been something to marvel at over the past few years. However, the concept of anonymous payouts has given cybercriminals a reason to be part of the game. They have developed crypto-mining malware that c...
Author: Ian Musyoka |
|
|
|
|
29
|
Cyberstalking and How to Protect Yourself From Identity Theft |

|
Image: Internet Security
Creating a better online experience in the data and communication field has become a non-negotiable topic. Given the current move into the digital space, advanced data platforms and new communication channels have been cre...
Author: Ian Musyoka |
|
|
|
|
30
|
Does private browsing actually work? |

|
With today's advanced technology, targeted ads and recommendation algorithms leave no space for privacy online. In line with this, you could expect your 'private' surfing through incognito mode to stay private, whereby you can remain anonymous. Howev...
Author: Collins Okoth |
|
|
|
|
31
|
What types of cyber-attacks and how to prevent them? |

|
Cyber-attacks are real problems that are here to stay, as long as the internet. It doesn’t matter whether you are an individual, organization, or business. Cybersecurity risks will catch up with you, now or soon. With the spread of connectivity relia...
Author: Faith Cheruiyot |
|
|
|
|
32
|
Can My Employer Monitor My Work Computer At Home? |

|
An employer has every right to monitor the work computers of their employees at home. The employer will do so for various reasons: they will need to ensure their employees' productivity. It is also for the protection of the organization's software ...
Author: Gloria Mutuku |
|
|
|
|
33
|
A Detailed Guide to Removing Ransomware in Windows 10 |
|
One of the main problems faced by internet companies today is Ransomware. For this reason, cybersecurity has continued to grow as an industry in general. Unfortunately, players on both sides can easily be described as the bad guys and the good guys. ...
Author: Collins Okoth |
|
|
|
|
34
|
How to Remove Malicious Software |

|
Malware is software designed to damage, gain access to, or disrupt the normal functioning of the computer. Malware is valuable to cybercriminals because they use it to extract sensitive information, prevent access to the device, and steal money. The ...
Author: Delilah Daut |
|
|
|
|
35
|
What Does a Firewall Do? |
|
Before I started writing this, I thought to myself, “Who really needs a firewall?” But, as it turns out, most of us do. If your personal or company computer is connected to the internet, your network is always exposed to threats and risks. This mea...
Author: Ian Musyoka |
|
|
|