|
1
|
Methods You Can Use to Protect Yourself from Social Engineering |

|
With the digital world evolving, the risk of social engineering has become a concern for many. Leveraging our expertise, we can arm you with methods to protect yourself against social engineering threats. This article will detail effective strategies...
Author: Newton Waweru |
|
|
|
|
2
|
What is a Possible Effect of Malicious Code |

|
Navigating the digital world can feel like a labyrinth, especially when malicious code lurks in the shadows. It's alarming, I know. But fear not; I've delved into this complex issue to help guide you. In this article, we'll illuminate the potential e...
Author: Newton Waweru |
|
|
|
|
3
|
Types of Cybersecurity Threats Identifying Key Risks |

|
Cybersecurity threats are a growing concern in our digital age, and staying informed is essential. As someone who understands your need for help, I've delved into this topic to provide you with valuable insights. This article will cover various cyber...
Author: Newton Waweru |
|
|
|
|
4
|
The Biggest Cybersecurity Attacks Recorded |

|
Curious about the world of cybersecurity? To keep you informed, I have delved into the most massive cyber attacks ever recorded. Let's explore the critical incidents, their impact, and ways to stay protected together. By the end of this article, you'...
Author: Newton Waweru |
|
|
|
|
5
|
Methods that Employees Can Expose Company Data Accidentally |

|
Concerned about employees accidentally exposing company data? You're not alone. I've delved into this issue, and I'm here to help. In this article, I'll explore standard methods that can lead to unintentional data leaks so that you can take preventiv...
Author: Newton Waweru |
|
|
|
|
6
|
The Danger of Mixing Cyberwarfare with Cyber Espionage |

|
Are you concerned about the potential hazards of combining cyber warfare and cyber espionage? You're not alone. As someone who has delved deep into this critical issue, I understand your concerns and am here to help. This article will explore the ris...
Author: Newton Waweru |
|
|
|
|
7
|
How to Protect Your Company Against Cyber Espionage |

|
Concerned about cyber espionage threatening your business? You're not alone. As an experienced researcher, I understand the need to stay vigilant. In this article, I'll explore practical steps to safeguard your company, providing you with the tools t...
Author: Newton Waweru |
|
|
|
|
8
|
Cybersecurity Expectations vs Reality What You Need to Know |

|
Are you eager to learn about cybersecurity but feel overwhelmed by the jargon and technicalities? You're not alone, as many people find themselves navigating this intricate landscape with high expectations, only to be met with realities that often fe...
Author: Newton Waweru |
|
|
|
|
9
|
The Next Big Thing in Cyber Security Discover Innovative Solutions |

|
Ready to uncover the Next Big Thing in Cyber Security? You're not alone! As cyber threats evolve, so should our defenses. Fear not, I've delved deep into this crucial issue to help you stay informed and prepared. Join me in this article as we explore...
Author: Newton Waweru |
|
|
|
|
10
|
What Does a Computer Repair Topeka KS Technicians Do |

|
Computer Repair Topeka, KS technicians perform all the necessary steps to repair the malfunctioning computer software and hardware. Upon calling a technician, they will first diagnose the issues with your computer system and ensure all are returned t...
Author: Tithi Raha |
|
|
|
|
11
|
How to Become a Technician For Computer Repair in Topeka, KS? |

|
A computer technician is responsible for repairing and maintaining all the computer equipment. Further, they repair hardware, update software, and troubleshoot any computer networks if required. However, becoming a technician for Computer Repair Tope...
Author: Tithi Raha |
|
|
|
|
12
|
What is The Difference Between Computer Repair Technicians & Help Desk |

|
When it comes to the help desk analyst and computer repair Topeka, KS technician, people often need clarification on these two. Regardless of how similar these two sound, they have significant differences. However, both of them are designed to help c...
Author: Tithi Raha |
|
|
|
|
13
|
The Career Outlook for a Computer Repair Technician in Topeka |

|
If you have a keen interest in learning the basics to complex concepts of computer systems, then becoming a Computer Repair Topeka, KS technician may be your primary career choice. However, in this competitive market, you may still wonder about the j...
Author: Tithi Raha |
|
|
|
|
14
|
Can Binary Code Be Used for Hacking? Uncover the Truth |

|
Are you eager to learn about the possibilities of using binary code for hacking? My comprehensive article explores the reality of binary code's capabilities in the realm of hacking.
In general, binary code can be applied as a technique in the field ...
Author: Newton Waweru |
|
|
|
|
15
|
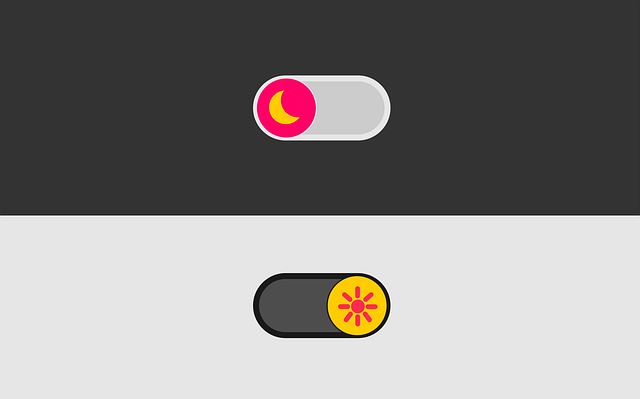
How to Turn on Google Chrome’s Dark Mode on Desktop and Mobile Devices |

|
How to Turn on Google Chrome's Dark Mode on Desktop and Mobile Devices
Although some people prefer using the Google Chrome browser in its standard light mode, others prefer the dark way, especially if they have underlying eye problems or working lat...
Author: James Fleming |
|
|
|
|
16
|
How Does Binary Code Work? The Basics of Binary Code |

|
Curious about the inner workings of binary code? Though it may appear daunting initially, the concepts are relatively basic. This guide delves into the fundamentals of binary code and its current applications. Suitable for both newbies and seasoned p...
Author: Newton Waweru |
|
|
|
|
17
|
Is Binary Code Hard To Learn? Become a Binary Code Expert |

|
It's okay; figuring out binary code doesn't have to be challenging! I've done some research on the subject and am here to assist. I comprehend the requirement to acquire new abilities and can direct you through the journey. In this piece, we'll delve...
Author: Newton Waweru |
|
|
|
|
18
|
The Ultimate Guide for Printing Out a Text Message Conversation |

|
The Ultimate Guide for Printing Out a Text Message Conversation
There are some messages you would want to keep. It could be because you need to produce them in court or because they are vital; hence you need them for good memories. For example, keep...
Author: James Fleming |
|
|
|
|
19
|
Does a DVI-D to HDMI connection carry audio?" |

|
Does a DVI-D to HDMI connection carry audio?
Introduction
Audio
This question has come up more than once. The short answer is no; it does not carry audio. The longer answer is that video and audio signals are two different types of signals, so con...
Author: James Fleming |
|
|
|
|
20
|
How to Put Your iPhone and iPad Into Dark Mode |
|
Enabling Dark Mode on your iPhone or iPad is not only a great way to save battery life, but it can also help reduce eye strain from intense light sources. It's an especially useful feature for those who find themselves using their device for prolon...
Author: James Fleming |
|
|
|
|
21
|
NFC Guide: All You Need to Know About Near Field Communication |

|
As technology advances and smartphones become practically ubiquitous, the need for Near Field Communication (NFC) is rapidly increasing. NFC allows two electronic devices to wirelessly communicate with each other when touching or just by being in c...
Author: James Fleming |
|
|
|
|
22
|
What are the Different Types of Tutorials? |

|
Do you always think about where you can learn how to do something? Most people look for tutorials to help them how to do tasks. Watching these videos gives you a deeper understanding and techniques for doing things better. It could be, installing ele...
Author: Faith Cheruiyot |
|
|
|
|
23
|
5 Things You Didn't Know About iPod Repair |

|
Apple's iPod is one of the most iconic devices in history. Though it may seem like it can't go wrong, accidents happen and iPods need to be repaired every so often.
There's a good chance th, at you have an iPod, or at least know someone who does. An...
Author: Faith Cheruiyot |
|
|
|
|
24
|
How In-home Computer Service Is Important to You |

|
There's no doubt that having a computer is important in this day and age. However, what happens when your computer breaks? Chances are you might not have the money to take it in for repair, or maybe you don't have the time to wait for it to be fixed....
Author: Faith Cheruiyot |
|
|
|
|
25
|
Where to Find Information on In-home Computer Service Online |

|
If you're like most people, your computer is an important part of your life. You use it for work, school, entertainment, and communication. When something goes wrong with it, it can be a huge inconvenience. Many people use in-home computer services i...
Author: Faith Cheruiyot |
|
|
|
|
26
|
What if I don't see a part I want in the custom Pc Builder? |

|
Want to build your PC or hire someone? Worry less, for there are several ways to learn and build your PC in just a few days. Before you start, it could be wise to understand this industry's basics and principles.
There are rules that a custom PC bui...
Author: Faith Cheruiyot |
|
|
|
|
27
|
What To Be Amazing At Monitor Screen Repair? Here's How |

|
Are you interested in getting into the monitor screen repair business? It's a great way to make some extra money and help people when needed. But how do you become amazing at screen repair?
There are a few tips to get you started: First, practice m...
Author: Faith Cheruiyot |
|
|
|
|
28
|
What is the Best Software for Making Video Tutorials? |

|
Are you planning to make video tutorials? Do you want to explain how your products and services function using the software? Video Tutorial software is ideal as it lets you edit, generate, manipulate and enhance videos. Such ensures the corporate and...
Author: Faith Cheruiyot |
|
|
|
|
29
|
What the Best Game Console Repair Pros Do (and You Should Too) |

|
Are you looking for things that game console repair experts do and wish you could? Here is a full guide to help you get more skills in the console repair industry.
As a whole, game console repair pros do things like cleaning, maintenance, and game c...
Author: Caroline Chebet |
|
|
|
|
30
|
Beginner Guide: How to Become an Ethical Hacker |

|
Dreaming to become an ethical hacker is one thing and becoming one in another one. It is not an easy ride in the park. The challenges and rough rides are part of the ethical hacker's journey. Allow me to take you the best ways to become an ethical ha...
Author: Berts Njoroge |
|
|
|
|
31
|
What things can you do on the dark web? |

|
Have you always wondered what goes on in the dark web? I understand your curiosity, and I am here to break down all you need to know about the dark. Anything in darkness will be brought to light, literally.
There are a lot of activities that happen...
Author: Berts Njoroge |
|
|
|
|
32
|
MS Word:How to Create and Manage a Table of Contents in Microsoft Word |

|
Have you ever tried to go through a numerous-page document that has no Table of Contents? It s such a hectic task to trace specific information that is way far in the paper. I found it essential to guide you through expert steps to create an excellen...
Author: Berts Njoroge |
|
|
|
|
33
|
Why does my computer keep freezing |

|
We all have faced a situation where you are using your computer at work, office, or school, and it happens- your computer randomly freezes. Your computer becomes useless, and you lose all the information on the projects at hand. I will guide you on h...
Author: Berts Njoroge |
|
|
|
|
34
|
What is the Internet of Things IoT |

|
The Internet of things (IoT) is a general term for the increasing number of electronics that are not conventional computer equipment but connected to the Internet to send information, receive instructions, or both.
Tech analyst company IDC forecasts...
Author: Collins Okoth |
|
|
|
|
35
|
Why Do We Need Ethics for Internet Users? |

|
With the introduction of computers globally in the 1990s, the entire approach of working, communicating, and storing important information has changed. I mean, who would have thought that a machine can make one convey a message at any corner of the w...
Author: Collins Okoth |
|
|
|