|
1
|
How have Online Scams Evolved Cybersecurity and Digital Deception |

|
Understanding the evolution of online scams is essential in this digital age. As someone who has thoroughly studied this issue, I share your concerns about this complex and ever-changing problem. This article is here to help, presenting a detailed lo...
Author: Newton Waweru |
|
|
|
|
2
|
Common Misconceptions about Cybersecurity |

|
It seems like you're curious about common misconceptions surrounding cybersecurity. Don't worry. I'm here to help you navigate this topic. As someone who has researched this extensively, this article will shed light on the most prevalent misunderstan...
Author: Newton Waweru |
|
|
|
|
3
|
What Is the Importance of Having a Strong Password Digital Protection |

|
Navigating the digital world, you may often wonder, "Why are strong passwords so crucial?" Passwords are your digital keys, guarding personal information and online identities. In this article, we'll delve into the importance of robust passwords to ...
Author: Newton Waweru |
|
|
|
|
4
|
How Can a Company Establish NonRepudiation Corporate Security Guide |

|
Let's delve into the concept of non-repudiation in a business context. It might seem intricate, but we're here to make it approachable. In this article, we'll explore proven strategies for your company to establish non-repudiation, providing confiden...
Author: Newton Waweru |
|
|
|
|
5
|
How Do Authentication Processes Work Decoding Security |

|
Hello there! The mechanics of digital authentication might seem complex. This is a vast topic, but I'm here to clarify it with my deep understanding. This article will delve into the functioning of authentication processes.
Authentication processes ...
Author: Newton Waweru |
|
|
|
|
6
|
Why Should You Avoid Public Wifi Protecting Your Online Privacy |

|
Navigating the web safely is more crucial than ever. You might wonder, "What's the harm in using public Wi-Fi?" This article will explore why avoiding public Wi-Fi can significantly enhance online security. Let's delve into the risks and precautions ...
Author: Newton Waweru |
|
|
|
|
7
|
Methods You Can Use to Protect Yourself from Social Engineering |

|
With the digital world evolving, the risk of social engineering has become a concern for many. Leveraging our expertise, we can arm you with methods to protect yourself against social engineering threats. This article will detail effective strategies...
Author: Newton Waweru |
|
|
|
|
8
|
What is a Possible Effect of Malicious Code |

|
Navigating the digital world can feel like a labyrinth, especially when malicious code lurks in the shadows. It's alarming, I know. But fear not; I've delved into this complex issue to help guide you. In this article, we'll illuminate the potential e...
Author: Newton Waweru |
|
|
|
|
9
|
How is Identity Theft Committed Technology |

|
Navigating the complex world of identity theft and technology can be daunting. Rest assured, I've thoroughly explored this landscape, and I'm here to guide you. This article unpacks how criminals exploit technology to commit identity theft, ensuring ...
Author: Newton Waweru |
|
|
|
|
10
|
The Next Big Thing in Cyber Security Discover Innovative Solutions |

|
Ready to uncover the Next Big Thing in Cyber Security? You're not alone! As cyber threats evolve, so should our defenses. Fear not, I've delved deep into this crucial issue to help you stay informed and prepared. Join me in this article as we explore...
Author: Newton Waweru |
|
|
|
|
11
|
Can Humans Read Binary Code Unlock the Secrets of Binary |

|
Have you ever wondered if humans can read binary code? If you're like many others, you may have encountered binary code in your computer science studies or even in your daily use of technology, but never quite understood how to read it. Well, you're ...
Author: Newton Waweru |
|
|
|
|
12
|
How Is the Information Passed Through Wires Key Techniques Revealed |

|
Discover the secrets of information transmission through wires. Are you curious about how data is transmitted across wires? Struggling to understand the technicalities? Don't worry, you're not alone.
As a whole, information is passed through wires u...
Author: Newton Waweru |
|
|
|
|
13
|
NFC Guide: All You Need to Know About Near Field Communication |

|
As technology advances and smartphones become practically ubiquitous, the need for Near Field Communication (NFC) is rapidly increasing. NFC allows two electronic devices to wirelessly communicate with each other when touching or just by being in c...
Author: James Fleming |
|
|
|
|
14
|
What Are Your Strategies To Avoid Being A Victim Of Cybercrime? |

|
Cybercrimes have been on the increase, with many unaware victims. When we hear about cybercrimes, we automatically think about hackers. But cybercrime is not just about hacking. It goes beyond that. Many people today use their devices, such as phones...
Author: James Fleming |
|
|
|
|
15
|
Bluetooth hacks: How to hack a car's Bluetooth? |

|
Bluetooth hacking is one of the most familiar hacks that hackers use. If you are a car owner, you must take precautions to keep your car safe from hackers. I want to keep myself and my car safe; that's why I researched and wrote this article to guide...
Author: Janet Kathalu |
|
|
|
|
16
|
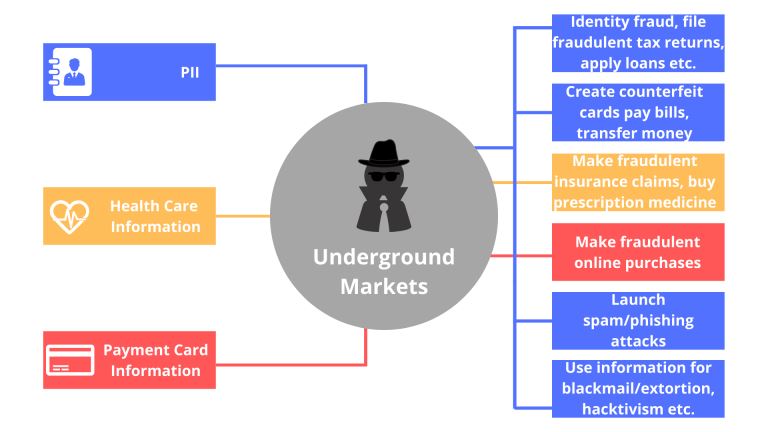
What things can you do on the dark web? |

|
Have you always wondered what goes on in the dark web? I understand your curiosity, and I am here to break down all you need to know about the dark. Anything in darkness will be brought to light, literally.
There are a lot of activities that happen...
Author: Berts Njoroge |
|
|
|
|
17
|
What Are the Signs a Website Has Been Hacked? |
|
If you own a business, you likely depend a lot on your website. From eCommerce to marketing, your website is the backbone of your transactions and everything in between. Without its help, you could face a lot of setbacks. Nevertheless, many business...
Author: Ian Musyoka |
|
|
|
|
18
|
Do I Really Need To Care About My Privacy Online? |
|
Online privacy seems almost non-existence when you factor in this age of likes, shares, tweets, and hashtags. Now more than ever, the activities of our daily lives are shared through social media. The worst part is that we are giving out this informa...
Author: Ian Musyoka |
|
|
|
|
19
|
What Happens When a Site I Use Gets Hacked? |

|
In the Internet’s virtual world, security is very confusing as compared to the real world. Security is messy; difficult to develop and sustain. As much as the Internet is built around a system of protocols, these rules can often be ignored.
When...
Author: Ian Musyoka |
|
|
|
|
20
|
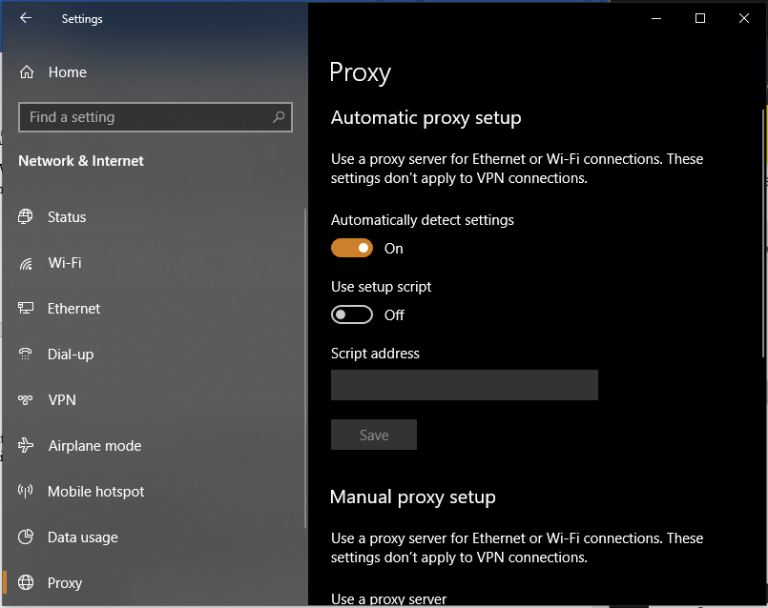
What are Proxy Server Ports? |
|
Proxy servers are dedicated software systems that run on a computer and are intermediaries between two endpoint devices. These endpoint devices are usually a personal computer and a server. A server is a central computer from which other computers (c...
Author: Collins Okoth |
|
|
|